Instagram Leaked Minors' PII Again, But Now It's Fixed
Data Breach Today
NOVEMBER 24, 2020
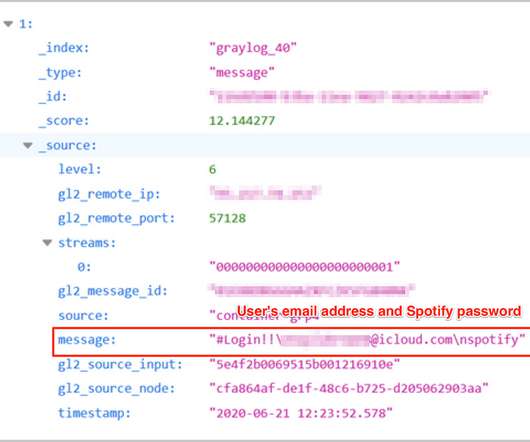
Exposure Comes as Ireland Probes Facebook's Handling of Children's Data For at least a month, Instagram leaked the email addresses of minors, which occurred as Ireland's Data Protection Commission probed whether its parent company, Facebook, failed to protect children's personal data. Facebook has fixed the issue. But how carefully is the company protecting personal data?




































Let's personalize your content