How 'Mespinoza' Ransomware Group Hits Targets
Data Breach Today
JULY 16, 2021
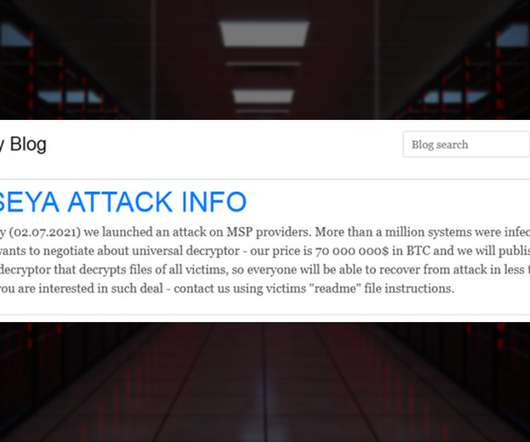
Palo Alto Networks Report Describes Tactics of Group Leveraging Open-Source Tools The gang behind the ransomware strain known as Mespinoza, aka PYSA, is targeting manufacturers, schools and others, mainly in the U.S. and U.K., demanding ransom payments as high as $1.6 million, according to Palo Alto Networks' Unit 42, which says the group leverages open-source tools.





































Let's personalize your content