CISA's Krebs: 2016 US Elections Were Cyber 'Sputnik' Moment
Data Breach Today
FEBRUARY 25, 2020
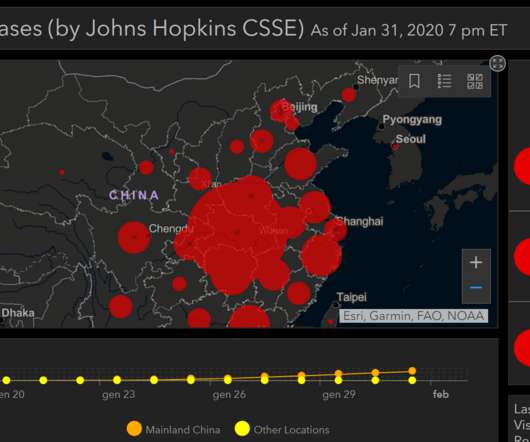
Cybersecurity Agency Ranks Election Security and Ransomware as Biggest Threats The 2016 U.S. presidential election served as a wake-up call for lawmakers and the public about the threat that cyber attackers can pose to the country's democracy, CISA Director Christopher Krebs told the 2020 RSA Conference. Election security and ransomware remain his agency's two biggest concerns.

































Let's personalize your content