Attackers Hacked into LastPass Via Employee's Home Computer
Data Breach Today
FEBRUARY 28, 2023
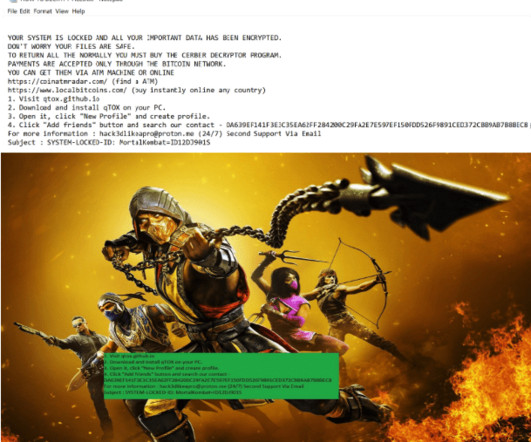
Attackers Exploited Vulnerability in Third-Party Software for Access The situation at LastPass keeps getting worse: the company says hackers implanted keylogger software on a DevOps employee's home computer to obtain access to the corporate vault. Customer vault data can be decrypted only with the end user master password, which LastPass doesn't store.






































Let's personalize your content