Apple’s Lockdown Mode Aims to Counter Spyware Threats
WIRED Threat Level
JULY 6, 2022
Starting with iOS 16, people who are at risk of being targeted with spyware will have some much-needed help.

WIRED Threat Level
JULY 6, 2022
Starting with iOS 16, people who are at risk of being targeted with spyware will have some much-needed help.

Data Breach Today
JULY 6, 2022
Swimlane Wants to Expand in Europe and Asia as well as Outside the Fortune 2000 Swimlane has raised $70 million to expand its clientele beyond the Fortune 2000 and acquire more customers in Europe and Asia-Pacific. The company plans to hire more personnel focused on sales, marketing and partnerships to make the company's low-code security automation platform accessible.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
JULY 6, 2022
Experts observed an increase in malicious activity targeting law enforcement agencies at the beginning of Q2 2022. Resecurity, a Los Angeles-based cybersecurity company protecting Fortune 500 companies worldwide, has registered an increase in malicious activity targeting law enforcement agencies at the beginning of Q2 2022. Threat actors are hacking email and other accounts which belong to police officers and their internal systems.

Data Breach Today
JULY 6, 2022
CISA, FBI, Treasury Department Issue Joint Alert About North Korean-Backed Attacks Federal authorities are alerting healthcare and public health sector entities of threats involving North Korean state-sponsored "Maui" ransomware. Attackers use the malware to maliciously encrypt diagnostics procedures, medical imaging, and medical center intranet services.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Dark Reading
JULY 6, 2022
The unsecured server exposed more than 1.5 million files, including airport worker ID photos and other PII, highlighting the ongoing cloud-security challenges worldwide.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

Adam Levin
JULY 6, 2022
A firewall is a network security device or program designed to prevent unauthorized and malicious internet traffic from entering a private network or device. It is a digital safety barrier between public and private internet connections, allowing non-threatening traffic in and keeping malicious traffic out, which in theory includes malware and hackers.

Data Breach Today
JULY 6, 2022
Bug Bounty Program An Experiment In Continuous Rewards For White Hats The U.S. Department of Defense continues to experiment with bug bounties to draw in vulnerability reports from outside white hat hackers. It kicked off a new test program for continuous rewards on America's Independence Day by setting aside a pool of $110,000.
Security Affairs
JULY 6, 2022
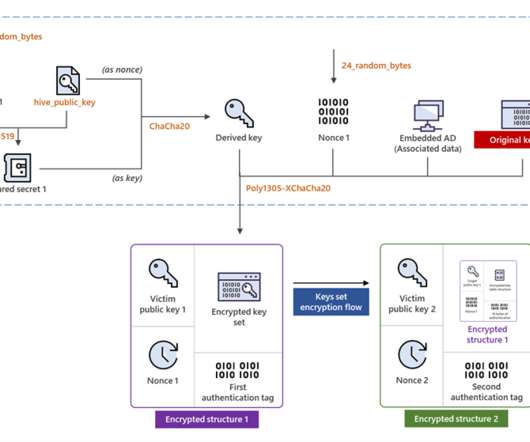
Hive ransomware operators have improved their file-encrypting module by migrating to Rust language and adopting a more sophisticated encryption method. The operators of the Hive ransomware upgraded their malware by migrating the malware to the Rust language and implementing a more sophisticated encryption method, Microsoft researchers warn. “The upgrades in the latest variant are effectively an overhaul: the most notable changes include a full code migration to another programming language

Troy Hunt
JULY 6, 2022
11 years now, wow 😲 It's actually 11 and a bit because it was April Fool's Day in 2011 that my first MVP award came through. At the time, I referred to myself as "The Accidental MVP" as I'd no expectation of an award, it just came from me being me. It's the same again today, and the last year has been full of just doing the stuff I love; loads of talks (which, like the one above at AusCERT, are actually starting to happen in front of real live humans again), l

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

IT Governance
JULY 6, 2022
Did you know that when presented with new information, we will forget half of it within a day? This is according to the Ebbinghaus forgetting curve , which theorises that people’s ability to recall facts decreases rapidly if there is no attempt to retain them. The effect begins almost immediately, and within a week we will have forgotten almost everything that we learned.

eSecurity Planet
JULY 6, 2022
MITRE has released its latest list of the top 25 most exploited vulnerabilities and exposures found in software. The MITRE CWE list is different from the product-specific CVE lists from the U.S. Cybersecurity and Infrastructure Security Agency (CISA) and other agencies and instead focuses on more generic software development weaknesses, similar to the OWASP list for web applications.

Schneier on Security
JULY 6, 2022
NIST’s post-quantum computing cryptography standard process is entering its final phases. It announced the first four algorithms: For general encryption, used when we access secure websites, NIST has selected the CRYSTALS-Kyber algorithm. Among its advantages are comparatively small encryption keys that two parties can exchange easily, as well as its speed of operation.

Jamf
JULY 6, 2022
At the most recent Cisco Live event, we saw a massive interest in Zero Trust Network Access (ZTNA) and solutions that empower remote workers. Read on and watch the video to learn about how Jamf Pro integrates with and extends Cisco’s enterprise networking solutions.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Dark Reading
JULY 6, 2022
They may be environmentally friendly, but the surging popularity of electric cars and plug-in hybrids puts the nation's electrical grid at greater risk for malfeasance.

KnowBe4
JULY 6, 2022
In an interesting extortion twist to get ransomware victims to pay up, one gang has created a search site to allow employees to see if their own private information has been made public.

Dark Reading
JULY 6, 2022
New research says IAM spending will grow on the back of affordable subscription services, spurred by cloud and mobile adoption, IoT, and continued remote working.

KnowBe4
JULY 6, 2022
Newly released data from TrendMicro about high-risk email threats in 2021 shows where cybercriminals are placing their focus and where yours should be as well.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Dark Reading
JULY 6, 2022
Our roundtable of cybersecurity experts weighs in on what makes QNAP network-attached storage catnip for attackers, and what organizations can do about it.
KnowBe4
JULY 6, 2022
The latest data on ransomware trends from backup vendor Veeam demonstrate the impact these attacks have on backups and an organization’s ability to recover.

Security Affairs
JULY 6, 2022
Hotel chain Marriott International suffered a new data breach, a threat actor has stolen 20GB from the company. Hotel chain Marriott International confirmed it has suffered a new data breach after a threat actor stole 20GB of files from one of its properties. The attacker compromised the network at the BWI Airport Marriott Maryland (BWIA), as confirmed later by the company.
Hanzo Learning Center
JULY 6, 2022
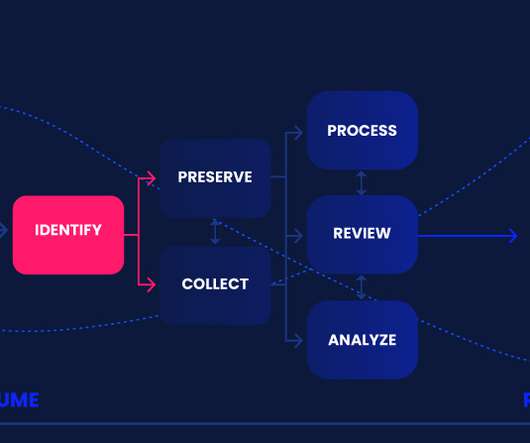
The eDiscovery Reference Model (EDRM) has been a long-established visualization of the eDiscovery process once litigation is anticipated.

Advertisement
If you’re considering migrating from DataStax Enterprise (DSE) to open source Apache Cassandra®, our comprehensive guide is tailored for architects, engineers, and IT directors. Whether you’re motivated by cost savings, avoiding vendor lock-in, or embracing the vibrant open-source community, Apache Cassandra offers robust value. Transition seamlessly to Instaclustr Managed Cassandra with our expert insights, ensuring zero downtime during migration.

Dark Reading
JULY 6, 2022
The hospitality giant said data from 300-400 individuals was compromised by a social-engineering scam targeting the Baltimore airport.

IG Guru
JULY 6, 2022
Check out the article here. The post Cybersecurity leaders are anticipating mass resignations within the year – here’s why via ZD Net appeared first on IG GURU.

Dark Reading
JULY 6, 2022
Apple's new Lockdown Mode protects devices targeted by sophisticated state-sponsored mercenary spyware attacks.

KnowBe4
JULY 6, 2022
Vade Secure warns that a phishing campaign is targeting TrustWallet cryptocurrency wallet users with phony verification emails.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Dark Reading
JULY 6, 2022
US government warns healthcare and public-health organizations to expect continued attacks involving the manually operated "Maui" ransomware.

Rocket Software
JULY 6, 2022
The Rocket® DevOps modernization platform helps businesses establish a robust DevOps infrastructure within existing multi-code environments that include IBM® i. By implementing DevOps operations onto existing platforms, teams are able to integrate innovative third-party tools and modernize existing processes to help increase productivity and easily improve regulatory compliance.

Threatpost
JULY 6, 2022
A developer appears to have divulged credentials to a police database on a popular developer forum, leading to a breach and subsequent bid to sell 23 terabytes of personal data on the dark web.
Let's personalize your content