The Iowa Caucus Tech Meltdown Is a Warning
WIRED Threat Level
FEBRUARY 4, 2020
The Iowa results will come in eventually, thanks to a paper trail. But it underscores just how much can go wrong when you lean on unnecessary, untested tech.

WIRED Threat Level
FEBRUARY 4, 2020
The Iowa results will come in eventually, thanks to a paper trail. But it underscores just how much can go wrong when you lean on unnecessary, untested tech.

Dark Reading
FEBRUARY 4, 2020
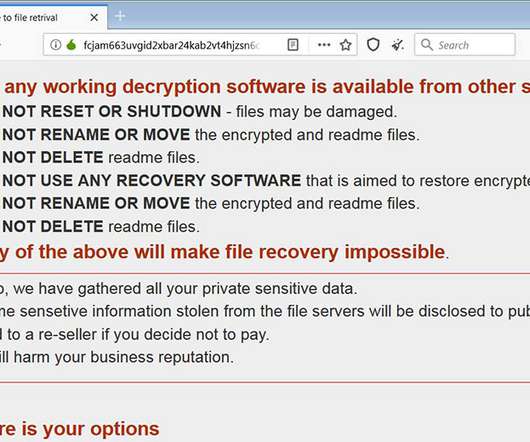
For cities, states and towns, paying up is short-sighted and only makes the problem worse.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Krebs on Security
FEBRUARY 4, 2020
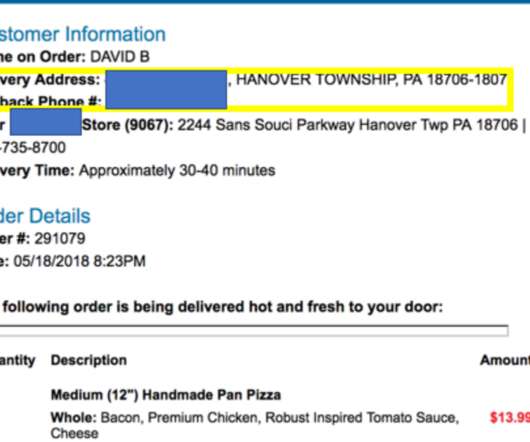
A Pennsylvania man who operated one of the Internet’s longest-running online attack-for-hire or “booter” services was sentenced to five years probation today. While the young man’s punishment was heavily tempered by his current poor health, the defendant’s dietary choices may have contributed to both his capture and the lenient sentencing: Investigators say the onetime booter boss’s identity became clear after he ordered a bacon and chicken pizza delivered to
Data Breach Today
FEBRUARY 4, 2020
Crypto-Locking Malware Gang Follows In Footsteps of Maze, Sodinokibi and Others More bad news for ransomware victims: Anyone hit with crypto-locking DoppelPaymer malware now faces the prospect of having their personal data dumped on a darknet site unless they pay a ransom. The gang's move follows in the footsteps of Maze, Sodinokibi (aka REvil) and Nemty ransomware operators.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.

Thales Cloud Protection & Licensing
FEBRUARY 4, 2020
The traditional focus on security has been on breach prevention and threat detection but these can only go so far. For organisations going through digital transformation there needs to be a layered approach to security – complimenting these traditional strategies with data protection.In the evolving digital world of cloud, social and apps, data is now the perimeter.
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

AIIM
FEBRUARY 4, 2020
You might think that here at AIIM we’d say everyone is a good candidate for the CIP designation. But, as the architect for the most recent updates to the Certified Information Professional (CIP) certification , a teacher of the CIP prep course, and a CIP pin-wearing member since its release in 2011, I don’t think it’s always a perfect fit. Here at AIIM, the last thing we want is for you to spend your time, money, and effort towards a certification that you won't be happy with in the end.

Data Breach Today
FEBRUARY 4, 2020
'State-Sponsored Actors' Might Be Behind Move to Map Phone Numbers to Accounts Twitter says it has fixed an API problem that would have allowed someone to match phone numbers en masse to a corresponding account, which could potentially unmask anonymous users. The flaw could have been found and exploited by state-sponsored actors, the social media firm warns.

The Guardian Data Protection
FEBRUARY 4, 2020
Investigation finds 400-plus councils let at least one third party track use of their sites Councils are sharing information about users of their websites – including when they seek help with a benefit claim, or with a disability or alcoholism – with dozens of private companies. More than 400 local authorities allowed at least one third-party company to track individuals who visit their sites, an investigation has revealed.

Data Breach Today
FEBRUARY 4, 2020
Phishing Techniques Used to Steal Credentials and Company Data A 21-year-old California man has pleaded guilty to repeatedly hacking gaming company Nintendo over three years to access servers and steal confidential data, including details on hardware, games and developer tools.

Advertisement
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

OpenText Information Management
FEBRUARY 4, 2020
In content and information management platforms, content is typically created and used internally to document projects, capture knowledge and provide compliance – all of which are important for a business to run smoothly. But how do these platforms actually drive positive change – both within an organization and in society? Content comes in many types, … The post Using information management for positive change appeared first on OpenText Blogs.

Data Breach Today
FEBRUARY 4, 2020
Streaming Site Joins Other Social Media Companies in Updating Policies YouTube has joined other social media companies in updating its content policies to help stop the spread of disinformation tied to the presidential election.

Information Management Resources
FEBRUARY 4, 2020
While digital technologies may improve the speed, efficiency and performance of operations, siloed or one-off projects alone won’t digitally transform an organization.

Data Breach Today
FEBRUARY 4, 2020
Concerns About the Use of the Technology in Public Places Persist The European Union appears to be moving toward dropping a temporary ban on the use of facial recognition technology in public places, according to news reports. Some technology experts had argued that a temporary ban would be impractical and ineffective in preventing abuse.

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Data Protection Report
FEBRUARY 4, 2020
On 21 January 2020 at a meeting at the World Economic Forum, the Personal Data Protection Commission ( PDPC ) and Infocommunications Media Development Authority ( IMDA ) released the second edition of its Model Artificial Intelligence (“ AI” ) Governance Framework (“ Model Framework” ). Background – the Model Framework. The Model Framework, which was first released in January 2019, is a voluntary set of compliance, ethical principles and governance considerations and recommendations that c

Security Affairs
FEBRUARY 4, 2020
A German artist demonstrated how using a simple trick it is possible to deceive Google Maps and create a virtual traffic jam. The German artist Simon Weckert conducted a simple experiment to demonstrat e how to deceive Google Maps and create a virtual traffic jam. The man put 99 cell mobile phones using Google Maps in a hand cart and started walking around the streets of Berlin.

Schneier on Security
FEBRUARY 4, 2020
The Norwegian Consumer Council has published an extensive report about how the adtech industry violates consumer privacy. At the same time, it is filing three legal complaints against six companies in this space. From a Twitter summary : 1. [thread] We are filing legal complaints against six companies based on our research, revealing systematic breaches to privacy, by shadowy #OutOfControl #adtech companies gathering & sharing heaps of personal data.

Security Affairs
FEBRUARY 4, 2020
Google has accidentally shared private videos of some users that were stored on its servers with other, the tech giant notified impacted users. Google admitted a new privacy incident, it has accidentally shared private videos saved on its servers with other users. At the time it is not clear the number of impacted users, anyway, the company sent them a security notification.

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

WIRED Threat Level
FEBRUARY 4, 2020
Your digital self is fragmented and owned by third parties. Kaliya Young has a plan to change that—and make tech fairer for all.

Data Protection Report
FEBRUARY 4, 2020
The CNIL has published draft recommendations on how to obtain consent when placing cookies. This is following the publication of its revised “Guidelines on the implementation of cookies or similar tracking technologies” which was published in July 2019 (see our article here ). The objective of the recommendations is to provide stakeholders with practical guidance and illustrative examples.
Security Affairs
FEBRUARY 4, 2020
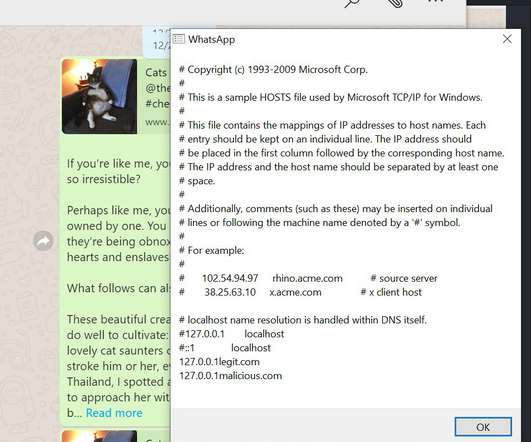
Facebook addressed a critical issue in WhatsApp that would have allowed attackers to read files from a user’s local file system, on macOS and Windows. Facebook has addressed a critical vulnerability in WhatsApp, tracked as CVE-2019-18426, that would have allowed hackers to read files from a user’s local file system, on macOS and Windows systems. “A vulnerability in WhatsApp Desktop when paired with WhatsApp for iPhone allows cross-site scripting and local file reading.

OpenText Information Management
FEBRUARY 4, 2020
OpenText™ is pleased to announce findings from a new report launched at Legaltech 2020 in conjunction with Ari Kaplan Advisors. The annual Next Generation Legal Operations report highlights the need to take control of eDiscovery costs, with AI, cloud and security all listed as top priorities for enterprise legal departments. Key findings from the survey … The post Cost, security and cloud are top priorities for legal departments appeared first on OpenText Blogs.

Advertisement
If you’re considering migrating from DataStax Enterprise (DSE) to open source Apache Cassandra®, our comprehensive guide is tailored for architects, engineers, and IT directors. Whether you’re motivated by cost savings, avoiding vendor lock-in, or embracing the vibrant open-source community, Apache Cassandra offers robust value. Transition seamlessly to Instaclustr Managed Cassandra with our expert insights, ensuring zero downtime during migration.

Security Affairs
FEBRUARY 4, 2020
The city of Racine joins to the long string of US municipalities that were hit with ransomware attack, it was forced offline following the infection. The city of Racine, Wisconsin, was hit with a ransomware, the incident took place on January 31, 2020. Most of non-emergency computer services of the city went offline following the attack. “City of Racine computer systems were infected by ransomware early Friday morning, and remained that way late Sunday afternoon.” reported the Govern

Threatpost
FEBRUARY 4, 2020
As part of its February bug fixes, Google is patching a critical severity remote code execution vulnerability and an information disclosure bug.

Security Affairs
FEBRUARY 4, 2020
Last week NCA arrested six individuals in the United Kingdom because they are suspected to be involved in a Malta cyber-heist and money laundering operation. Britain’s National Crime Agency (NCA) arrested six individuals in the United Kingdom because they are accused to be involved in a cyber-heist of a Malta bank and money laundering operation.

Dark Reading
FEBRUARY 4, 2020
Thousands of servers could be exposed to SharePoint vulnerability CVE-2019-0604, recently used in cyberattacks against Middle East government targets.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Hunton Privacy
FEBRUARY 4, 2020
On February 1, 2020, the Italian Data Protection Authority ( Garante per la protezione dei dati personali , the “Garante”) announced that it had levied a fine of €27,802,946 on TIM S.p.A. (“TIM”), a telecommunications company, for several unlawful marketing data processing practices. Between 2017 and 2019, the Garante received numerous complaints from individuals (including from individuals who were not existing customers of TIM) claiming that they had received unwanted marketing calls, without

Dark Reading
FEBRUARY 4, 2020
Here's what small and midsize businesses should consider when they decide it's time to up their website security.

Security Affairs
FEBRUARY 4, 2020
The Australian transportation and logistics giant Toll Group has suffered a ransomware attack that forced it to shut down part of its services. The Australian transportation and logistics giant Toll Group was victim of a ransomware attack, in response to the incident the company has shut down some of its online services. The Toll Group is an Australian transportation and logistics company with operations in road, rail, sea, air, and warehousing, it is a subsidiary of Japan Post Holdings and has
Let's personalize your content