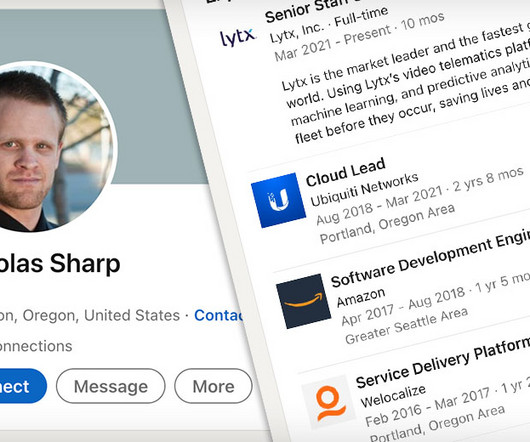
Ubiquiti Insider Hacker Sentenced to 6 Years in Prison
Data Breach Today
MAY 10, 2023
Nickolas Sharp, 37, Must Also Pay $1.6 Million In Restitution Nickolas Sharp, a one-time employee of Ubiquity who pleaded guilty to insider hacking received Wednesday a six year prison sentence. He admitted guilt on Feb. 2 to three criminal counts including transmitting a program to a protected computer that intentionally caused damage.




































Let's personalize your content