Intel, AMD Dispute Findings on Chip Vulnerabilities
Data Breach Today
MAY 6, 2021
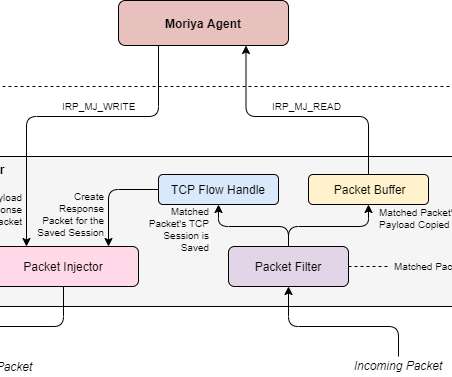
After Researchers Release Report, Chipmakers Assert That No New Defenses Are Needed Intel and AMD are disputing the findings of researchers from two universities who say they've discovered new attacks on Intel and AMD processors that can bypass most of the defenses put in place earlier for similar "Spectre" and "Meltdown" attacks.








































Let's personalize your content