FBI Warns of Uptick in Ragnar Locker Ransomware Activity
Data Breach Today
NOVEMBER 25, 2020
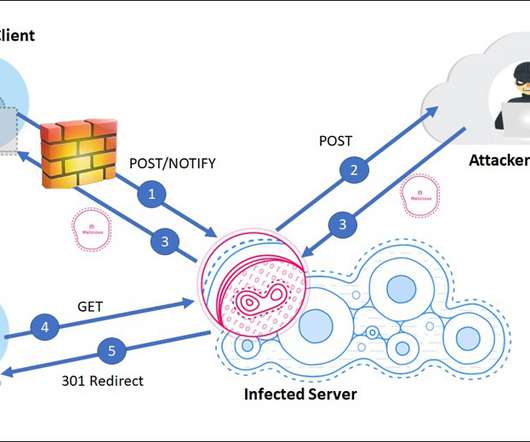
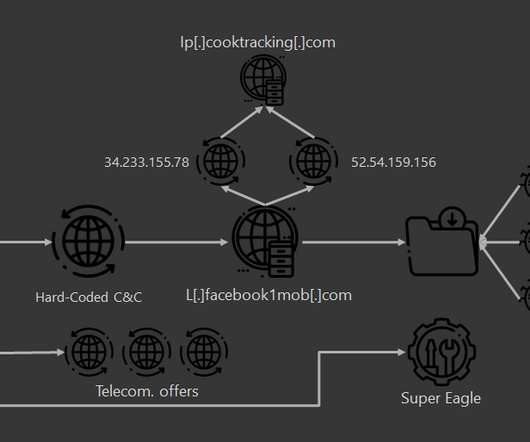
Bureau Says the Attacks Are Hitting Many Sectors The FBI has sent out a private industry alert warning about increasing attacks using Ragnar Locker ransomware. The operators behind this crypto-locking malware have recently targeted companies that include EDP, Campari and Capcom, researchers note.




































Let's personalize your content