Another Threat Group Joins Ransomware Extortion Racket
Data Breach Today
OCTOBER 15, 2020
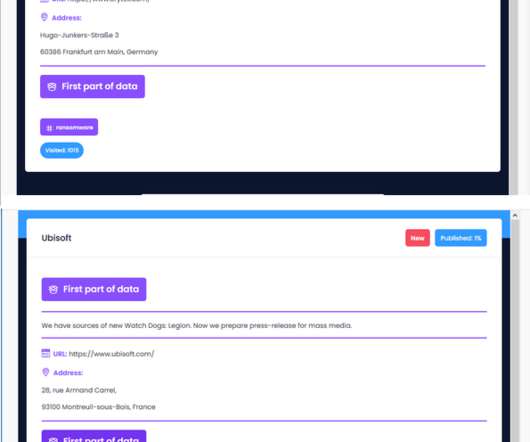
FireEye: 'FIN11' Deploys Clop Ransomware A newly identified financially motivated threat group, dubbed "FIN11," is deploying Clop ransomware and exfiltrating data from its targets for extortion efforts, according to researchers at FireEye Mandiant.





































Let's personalize your content