A Dangerous Year in America Enters Its Most Dangerous Month
WIRED Threat Level
OCTOBER 5, 2020
Seven distinct factors between now and the election threaten to combine, compound, and reinforce each other in unpredictable ways.

WIRED Threat Level
OCTOBER 5, 2020
Seven distinct factors between now and the election threaten to combine, compound, and reinforce each other in unpredictable ways.

Data Breach Today
OCTOBER 5, 2020
Employee Surveillance Violations Trigger Germany's Biggest Privacy Fine to Date Privacy regulators in Germany have slammed clothing retailer H&M with a $41 million fine for collecting and retaining private employee data in violation of the EU's General Data Protection Regulation. H&M has apologized, instituted changes and promised to financially compensate employees.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Security Affairs
OCTOBER 5, 2020
Threat actors have hacked at least three Swiss universities, including the University of Basel and managed to drain employee salary transfers. Threat actors have managed to steal employee salary payments at several Swiss universities, including the University of Basel. “According to our information, several universities in Switzerland have been affected,” explained Martina Weiss, Secretary General of the Rectors’ Conference of the Swiss Universities.

Data Breach Today
OCTOBER 5, 2020
In an exclusive interview, Roger Severino, director of the HHS Office for Civil Rights, which enforces HIPAA, spells out critical steps healthcare organizations must take to safeguard patient information and ensure patient safety in light of the surge in ransomware and other hacking incidents.

Speaker: Aarushi Kansal, AI Leader & Author and Tony Karrer, Founder & CTO at Aggregage
Software leaders who are building applications based on Large Language Models (LLMs) often find it a challenge to achieve reliability. It’s no surprise given the non-deterministic nature of LLMs. To effectively create reliable LLM-based (often with RAG) applications, extensive testing and evaluation processes are crucial. This often ends up involving meticulous adjustments to prompts.
Security Affairs
OCTOBER 5, 2020
Security researchers provided technical details about an IoT botnet dubbed Ttint that has been exploiting two zero-days in Tenda routers. Security researchers at Netlab, the network security division Qihoo 360, have published a report that details an IoT botnet dubbed Ttint. The experts are monitoring the Mirai-based botnet since November 2019 and observed it exploiting two Tenda router 0-day vulnerabilities to spread a Remote Access Trojan (RAT).
Information Management Today brings together the best content for information management professionals from the widest variety of industry thought leaders.

National Archives Records Express
OCTOBER 5, 2020
Last week, our office released two NARA Bulletins for Federal agencies. The first, NARA Bulletin 2020-01 , is the guidance answering common questions and providing clarifications to the OMB/NARA Memorandum M-19-21 : Transition to Electronic Records. This Bulletin is the additional guidance required by the Memorandum. . We have received many questions from agencies, including general questions, exception process questions, records storage facility questions, and scheduling and transfer questions

Data Breach Today
OCTOBER 5, 2020
Author Ivana Bartoletti on Why Privacy Protection Is Essential to a Company's Survival Organizations in all sectors need to end "the dichotomy between privacy and security" and avoid a checklist approach to privacy protection, says digital ethics expert Ivana Bartoletti, who explains why ensuring customers' privacy is essential to a company's survival.

Schneier on Security
OCTOBER 5, 2020
Interesting usability study: “ More Than Just Good Passwords? A Study on Usability and Security Perceptions of Risk-based Authentication “: Abstract : Risk-based Authentication (RBA) is an adaptive security measure to strengthen password-based authentication. RBA monitors additional features during login, and when observed feature values differ significantly from previously seen ones, users have to provide additional authentication factors such as a verification code.

Data Breach Today
OCTOBER 5, 2020
Black-T Malware Favors Targeting AWS credential files A new malware variant dubbed Black-T developed by the hacker group TeamTnT targets exposed Docker daemon APIs to perform scanning and cryptojacking operations, according to researchers at Palo Alto Networks' Unit 42.

Advertisement
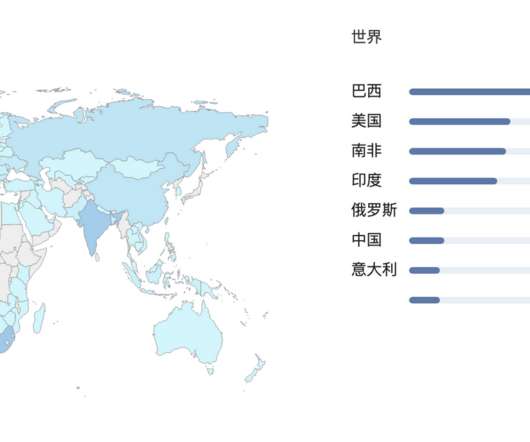
Geopolitical risk is now at the top of the agenda for CEOs. But tracking it can be difficult. The world is more interconnected than ever, whether in terms of economics and supply chains or technology and communication. Geopolitically, however, it is becoming increasingly fragmented – threatening the operations, financial well-being, and security of globally connected companies.

IT Governance
OCTOBER 5, 2020
Are you trying to figure out the best way to protect your organisation from cyber attacks and data breaches? It can be tricky to know where to begin, which is why our Cyber Security Risk Scorecard contains a simple guide to help you secure your systems. We’ve run through some of the essential steps in this blog, or download the full, free checklist from our website.

Data Breach Today
OCTOBER 5, 2020
Digital identity is coming of age as a way to enable COVID-19 contact tracing, crack down on payment fraud and much more, says Tony Craddock of the Emerging Payments Association.
Security Affairs
OCTOBER 5, 2020
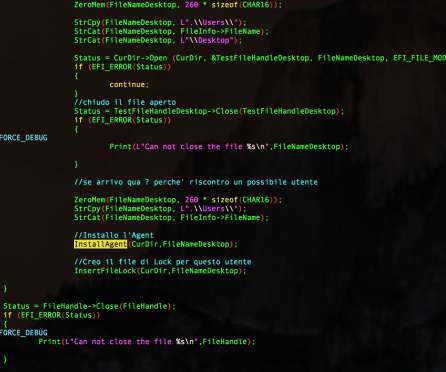
A China-linked threat actor used UEFI malware based on code from Hacking Team in attacks aimed at organizations with an interest in North Korea. Researchers from Kaspersky have spotted a UEFI malware that was involved in attacks on organizations with an interest in North Korea. The experts were investigating several suspicious UEFI firmware images when discovered four components, some of which were borrowing the source code a Hacking Team spyware.

OpenText Information Management
OCTOBER 5, 2020
It’s no secret that today’s global supply chain is more complex than ever. It has become a digital ecosystem of suppliers, logistics companies, customers and other value chain partners that stretch across the globe. The supply chain relies on the synchronized movement of thousands of interrelated parts to meet growing customer demand for better, more … The post What is a connected supply chain?

Advertisement
Apache Cassandra is an open-source distributed database that boasts an architecture that delivers high scalability, near 100% availability, and powerful read-and-write performance required for many data-heavy use cases. However, many developers and administrators who are new to this NoSQL database often encounter several challenges that can impact its performance.

Security Affairs
OCTOBER 5, 2020
Cybernews has found an exposed data bucket that belongs to the Australian news sharing platform Snewpit containing around 80,000 user records. Original post at [link]. To increase efforts to secure user data, Snewpit will be reviewing “all server logs and access control settings” to confirm that no unauthorized access took place and to ensure that “user data is secure and encrypted.”.
Hunton Privacy
OCTOBER 5, 2020
On October 1, 2020, the French Data Protection Authority (the “CNIL”) published a revised version of its guidelines on cookies and similar technologies (the “Guidelines”), its final recommendations on the practical modalities for obtaining users’ consent to store or read non-essential cookies and similar technologies on their devices (the “Recommendations”) and a set of questions and answers on the Recommendations (“FAQs”).

Security Affairs
OCTOBER 5, 2020
Researchers disclosed details of security flaws in popular antivirus software that could allow threat actors to increase privileges. Security researchers from CyberArk Labs disclosed details of security vulnerabilities found in popular antivirus software that could be exploited by attackers to elevate their privileges on the target system. Antivirus solutions that are supposed to protect the systems from infection may unintentionally allow malware in escalating privileges on the system. .

DXC Technology
OCTOBER 5, 2020
??????????????????????????????1?4,000????????10???????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????????? ??????????????????????????????????????????????????????????????????ClinicalWorks???????????/ADR????????? ClinicalWorks/ADR??DXC?????????????????DEC?????????????????????????????????????????

Advertisement
“Reimagined: Building Products with Generative AI” is an extensive guide for integrating generative AI into product strategy and careers featuring over 150 real-world examples, 30 case studies, and 20+ frameworks, and endorsed by over 20 leading AI and product executives, inventors, entrepreneurs, and researchers.

Security Affairs
OCTOBER 5, 2020
U.S. DoD and the DHS CISA agency published a malware analysis report for a new malware variant tracked as SLOTHFULMEDIA. The U.S. Department of Defense’s Cyber National Mission Force (CNMF) and the Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency (CISA) have published a malware analysis report that provides technical details of a new dropper tracked as SLOTHFULMEDIA.

CGI
OCTOBER 5, 2020
Central banking in the 2020s. This CGI blog post discusses what a next-generation central banking architecture will look like. shobana.lv@cgi.com. Mon, 10/05/2020 - 03:15.

Data Protection Report
OCTOBER 5, 2020
On 1 October 2020, the State Commissioner for Data Protection and Freedom of Information (Landesbeauftragte für Datenschutz und Informationsfreiheit) of Hamburg (the DPA) imposed a fine of EUR 35.3 million under the GDPR against the German subsidiary of the fashion retailer H&M. The German subsidiary operates a central service centre in Nuremberg.

Dark Reading
OCTOBER 5, 2020
A new initiative will run throughout the month of October, invites the general public to play cybersecurity games (and win fabulous prizes).

Advertisement
If you’re considering migrating from DataStax Enterprise (DSE) to open source Apache Cassandra®, our comprehensive guide is tailored for architects, engineers, and IT directors. Whether you’re motivated by cost savings, avoiding vendor lock-in, or embracing the vibrant open-source community, Apache Cassandra offers robust value. Transition seamlessly to Instaclustr Managed Cassandra with our expert insights, ensuring zero downtime during migration.
Threatpost
OCTOBER 5, 2020
A variant of the Mirai botnet, called Ttint, has added espionage capabilities to complement its denial-of-service functions.

Dark Reading
OCTOBER 5, 2020
Critical Android vulnerability CVE-2019-2234 could enable attackers to take control of a victim's camera and take photos, record videos, and learn location.
Threatpost
OCTOBER 5, 2020
Team Showcase, a sister plugin, is also vulnerable to the XSS and PHP object-injection bugs -- together they have 66,000 installs.
WIRED Threat Level
OCTOBER 5, 2020
The tool attacks a device’s UEFI firmware—which makes it especially hard to detect and destroy.

Advertisement
Are you trying to decide which entity resolution capabilities you need? It can be confusing to determine which features are most important for your project. And sometimes key features are overlooked. Get the Entity Resolution Evaluation Checklist to make sure you’ve thought of everything to make your project a success! The list was created by Senzing’s team of leading entity resolution experts, based on their real-world experience.

Threatpost
OCTOBER 5, 2020
The two alleged leaders of Team Xecuter targeted popular consoles like the Nintendo Switch, the Sony PlayStation Classic and Microsoft Xbox.

Dark Reading
OCTOBER 5, 2020
The battle's just beginning as bad actors glean more personal information from victims and use that data to launch larger attacks.

OpenText Information Management
OCTOBER 5, 2020
In January, I wrote a predictions blog that said the priorities of the financial services industry would not change greatly over the next 12 months! Of course, no one could have seen the full extent of the global COVID-19 crisis, but as we navigate through the pandemic it’s time to re-assess those trends and see how things have evolved. Welcome to the world of home working In my previous predictions blog, Jim Marous, Owner … The post Key financial services trends as the world emerges fr
Let's personalize your content