Iran-linked Lyceum APT adds a new.NET DNS Backdoor to its arsenal
Security Affairs
JUNE 11, 2022
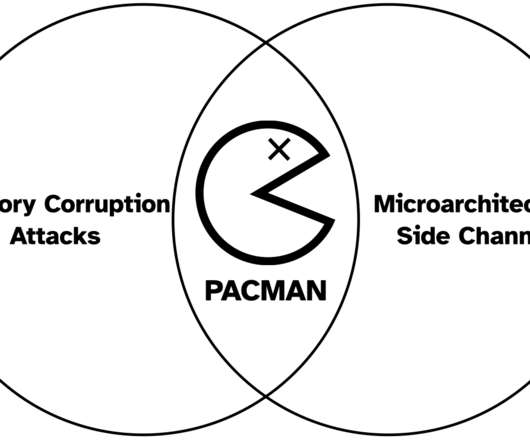
Iran-linked Lyceum APT group uses a new.NET-based DNS backdoor to target organizations in the energy and telecommunication sectors. The Iran-linked Lyceum APT group, aka Hexane or Spilrin, used a new.NET-based DNS backdoor in a campaign aimed at companies in the energy and telecommunication sectors, ZScaler researchers warn. The activity of the Lyceum APT group was first documented earlier in August 2019 by researchers at ICS security firm Dragos which tracked it as Hexane.








Let's personalize your content