Defense Department Agency Reports Data Breach
Data Breach Today
FEBRUARY 21, 2020
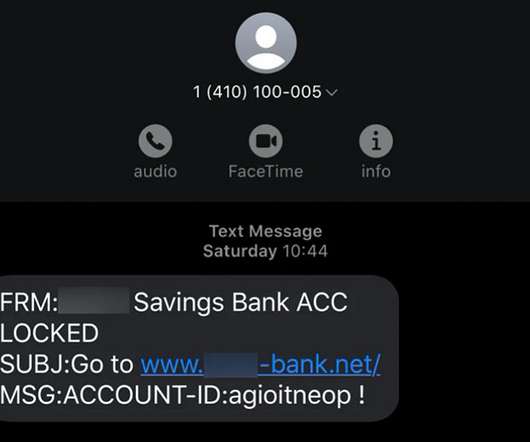
Defense Information Systems Agency Has a Security Mission A U.S. Defense Department agency that's responsible for providing secure communications and IT equipment for the president and other top government officials says a data breach of one of its systems may have exposed personal data, including Social Security numbers.



































Let's personalize your content