Ransomware Reminder: Paying Ransoms Doesn't Pay
Data Breach Today
MAY 14, 2020
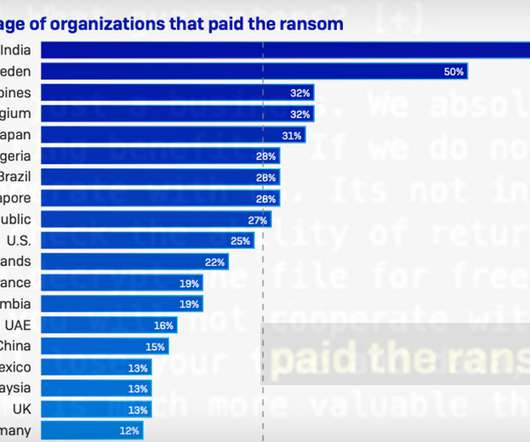
Funding Criminals Perpetuates Cybercrime Security experts and law enforcement officials have long argued that paying ransoms doesn't pay. For starters, it directly funds the cybercrime ecosystem and makes it attractive for criminals to keep launching ransomware attacks.


































Let's personalize your content