Chinese APT Using Google Drive, Dropbox to Drop Malware
Data Breach Today
NOVEMBER 21, 2022
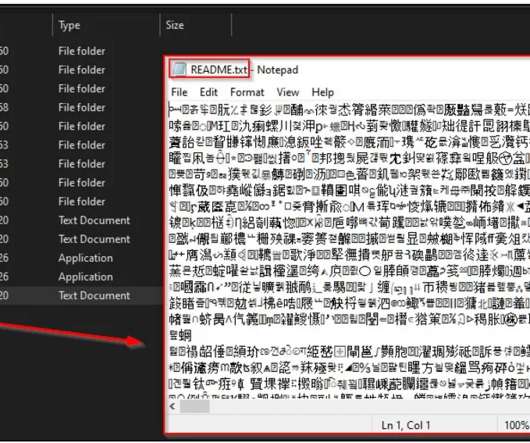
Evolved Mustang Panda Malware Targets Government, Education, Other Sectors Globally A large-scale cyberespionage campaign by notorious China-based advanced persistent threat actor Mustang Panda is targeting government, academic and other sectors globally. Its main targets include Asia-Pacific organizations in Myanmar, Australia, the Philippines, Japan and Taiwan.




































Let's personalize your content