Phishing Attack Bypassed Office 365 Multifactor Protections
Data Breach Today
MAY 20, 2020
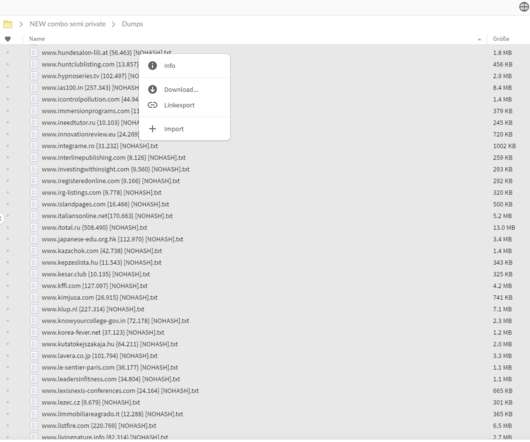
Researchers: Campaign Designed to Steal Users' Credentials, Launch Other Attacks A recent phishing campaign bypassed multifactor authentication protections within Microsoft Office 365 to steal users' credentials stored in the cloud or launch other attacks, according to the security firm Cofense.


































Let's personalize your content