Co-Creator of Site That Sold Payment Card Data Pleads Guilty
Data Breach Today
JUNE 29, 2020
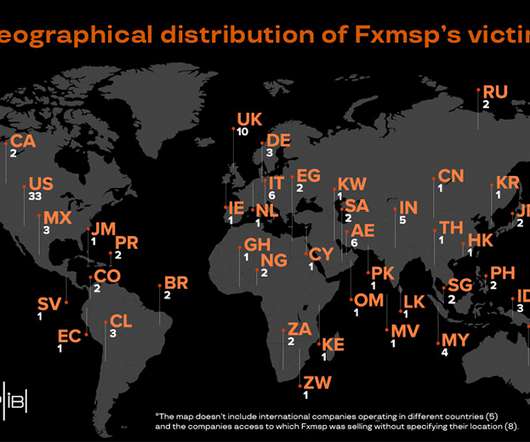
Infraud Organization's Site, Shuttered in 2018, Tied to $530 Million in Fraud A Russian national charged in connection with co-creating the Infraud Organization's online cybercrime forum that sold stolen payment card data and was tied to $530 million in fraud losses has pleaded guilty.

































Let's personalize your content