COVID-19 Drives Spike in Mobile Phishing Attacks: Report
Data Breach Today
JUNE 4, 2020
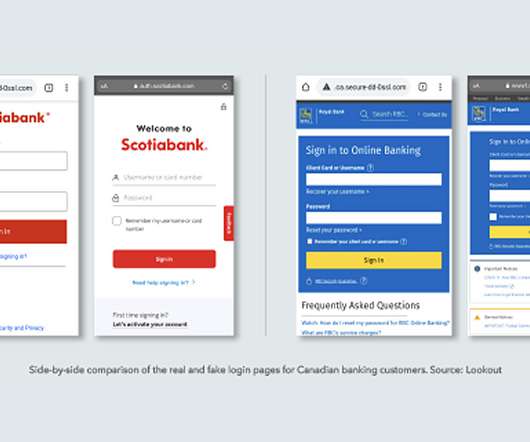
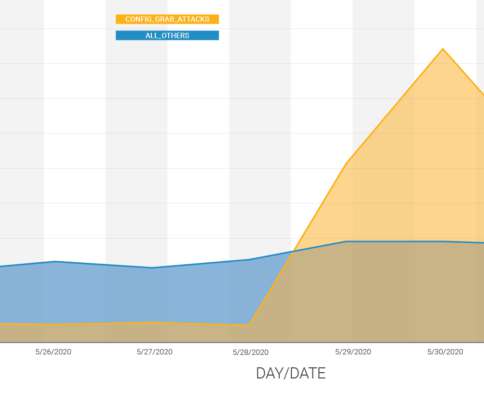
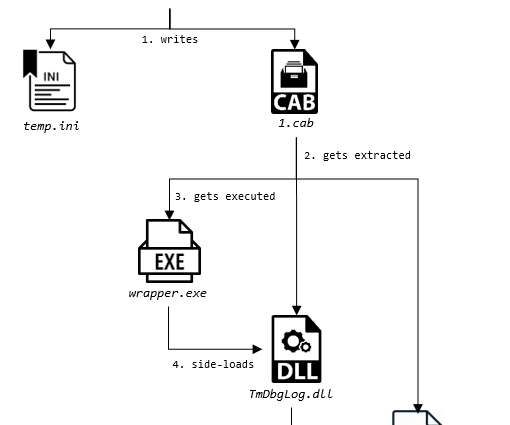
Researchers Say Targeted Campaigns Are Spoofing Banks' Login Sites The shift to working from home during the COVID-19 pandemic has led to an increase in mobile phishing campaigns, with attackers targeting remote workers whose devices lack adequate security protections, according to the security firm Lookout. Many of these campaigns are designed to steal users' banking credentials.




































Let's personalize your content