Google warned 12K+ users targeted by state-sponsored hackers
Security Affairs
DECEMBER 1, 2019
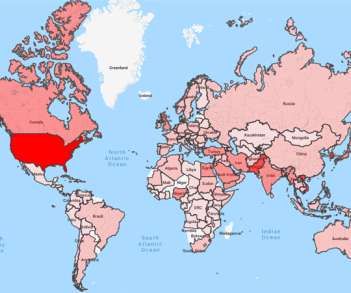
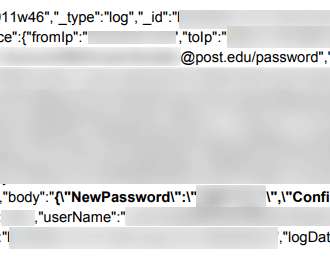
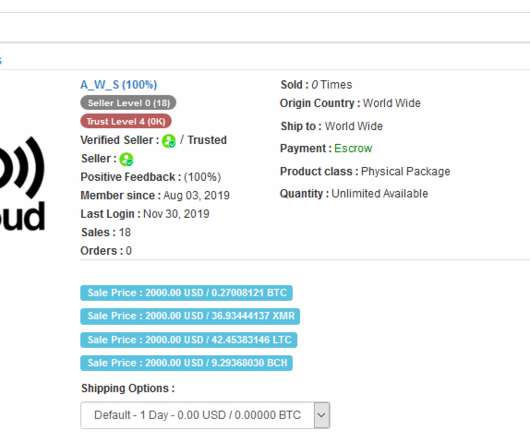
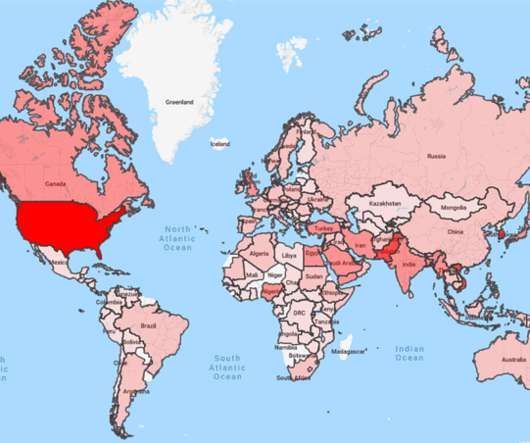
Google revealed that over 12,000 of its users were targeted by state-sponsored hackers in the third quarter of this year. Google’s Threat Analysis Group (TAG) revealed that it has detected and blocked attacks carried out by nation-state actors on 12,000 of its users in the third quarter of this year. Over 90 percent of the users identified by Google were targeted via “credential phishing emails” that attempt to trick victims into providing their password or other account credentials to hij

















Let's personalize your content