EU Proposes Joint Cybersecurity Unit
Data Breach Today
JUNE 23, 2021
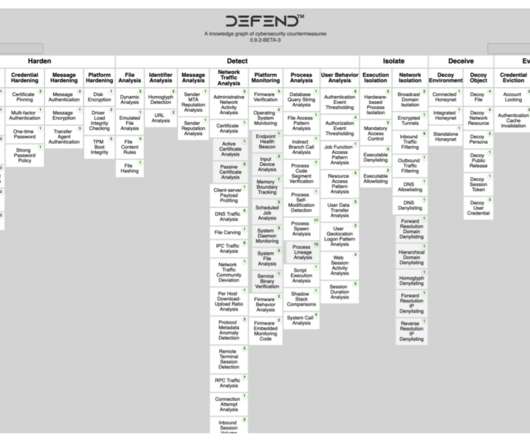
Agency Would Help Member States Respond to Cyberattacks The European Commission has proposed creating a Joint Cyber Unit to help EU member states respond to and prevent cyberattacks, especially those involving ransomware. The goal is for the unit to begin operations by the end of next year.




































Let's personalize your content