Stolen Cards, Reportedly From Cardpool.com, Sold on Darknet
Data Breach Today
APRIL 6, 2021
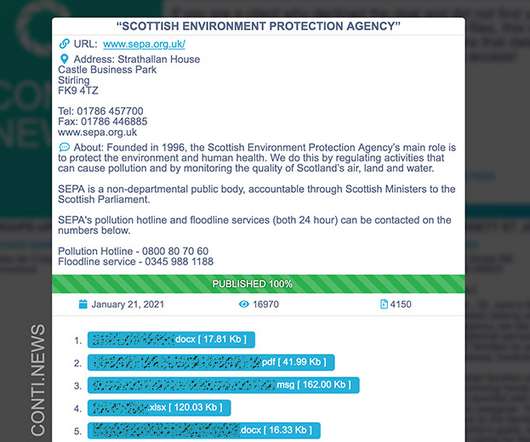
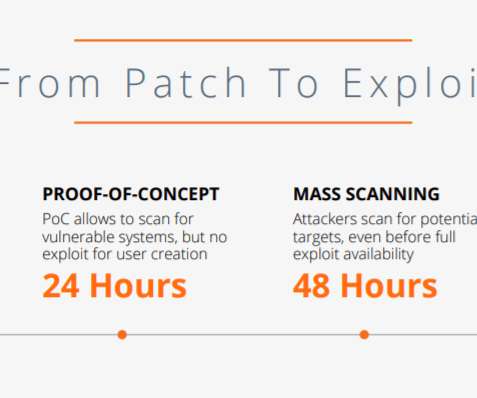
Gemini Advisory Says Russian Cybercriminal Sold Gift Card, Payment Card Data A Russian-speaking cybercriminal recently sold on a darknet forum thousands of stolen payment and gift cards that researchers at Gemini Advisory believe were taken from the now defunct online gift card exchange Cardpool.com.
































Let's personalize your content