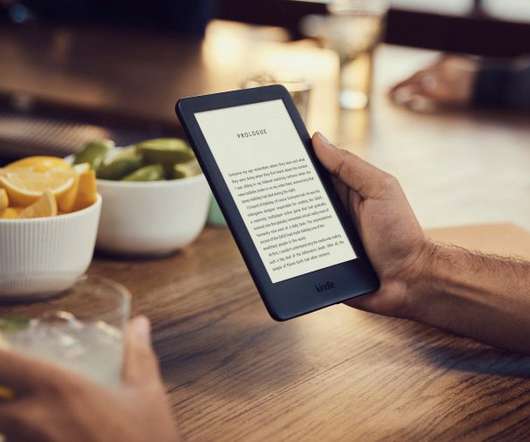
FBI seized other domains used by the shadow eBook library Z-Library
Security Affairs
MAY 6, 2023
The FBI disrupted once again the illegal eBook library Z-Library the authorities seized several domains used by the service. The Federal Bureau of Investigation (FBI) seized multiple domains used by the illegal shadow eBook library Z-Library. We are in the final!












































Let's personalize your content