Free Tool Unlocks Some Encrypted Data in Ransomware Attacks
Dark Reading
MAY 10, 2023
"White Phoenix" automated tool for recovering data on partially encrypted files hit with ransomware is available on GitHub.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Dark Reading
MAY 10, 2023
"White Phoenix" automated tool for recovering data on partially encrypted files hit with ransomware is available on GitHub.

Data Breach Today
JANUARY 6, 2021
National Security Agency has released guidance on how the Defense Department, other federal agencies and the contractors that support them should replace obsolete encryption protocols that can enable cyber intrusions. Agency Recommends Replacement of Old TLS and SSL Protocols The U.S.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

Data Breach Today
APRIL 22, 2021
Flaws Described by Moxie Marlinspike Raise Questions About Extracted Data's Trustworthiness Law enforcement agencies use forensics tools from Israeli company Cellebrite to gain access to locked mobile devices and extract data.
Krebs on Security
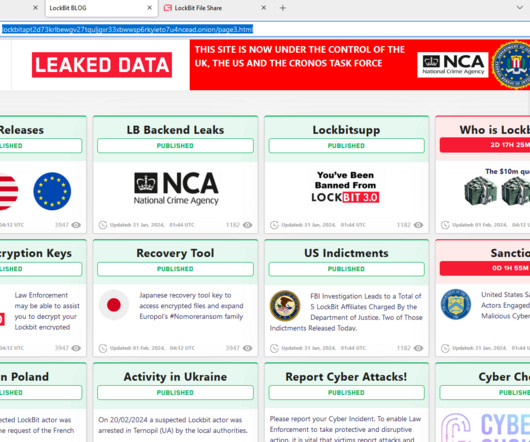
FEBRUARY 20, 2024
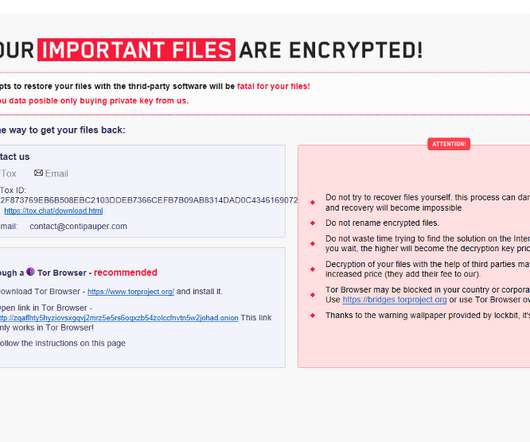
Instead of listing data stolen from ransomware victims who didn’t pay, LockBit’s victim shaming website now offers free recovery tools, as well as news about arrests and criminal charges involving LockBit affiliates. Black Ransomware.

Data Breach Today
MAY 11, 2023
Also: Twitter Hacker Pleads Guilty, Seoul National University Hospital and Sysco In this week's data breach, the spotlight was on Dragos, a guilty plea from a Twitter hacker and cryptocurrency thief and North Korean hackers. Plus, a new tool for decrypting partially encrypted files.

Data Breach Today
NOVEMBER 20, 2020
Romanians Allegedly Ran 'CyberSeal,' 'Dataprotector' and 'Cyberscan' Services Europol has arrested two Romanians for allegedly selling services - including malware encryption - that helped cybercriminals circumvent antivirus tools.

eSecurity Planet
AUGUST 4, 2022
It’s been a couple of decades since data tapes delivered by trucks made encryption a standard enterprise cybersecurity practice. Yet even as technology has changed, sending and receiving data remains a major vulnerability, ensuring encryption’s place as a foundational security practice. What is Encryption?

Data Breach Today
DECEMBER 22, 2020
Move Seen as Alternative to Weakening Encryption Europol, the European Union's law enforcement agency, and the European Commission are launching a new decryption platform to help law enforcement agencies decrypt data that has been obtained as part of a criminal investigation, a move seen as an alternative to weakening encryption.

Schneier on Security
JULY 2, 2019
Google has released an open-source cryptographic tool: Private Join and Compute. From a Wired article : Private Join and Compute uses a 1970s methodology known as "commutative encryption" to allow data in the data sets to be encrypted with multiple keys, without it mattering which order the keys are used in.

Thales Cloud Protection & Licensing
JANUARY 31, 2024
ESG Research Unearths Critical Insights for Future-Proofing Encryption and Key Management madhav Thu, 02/01/2024 - 05:14 Encryption and key management are critical defenses against data breaches and cyber threats in the evolving digital landscape. This trend underscores the growing reliance on encryption as a primary safeguard.

eSecurity Planet
SEPTEMBER 22, 2022
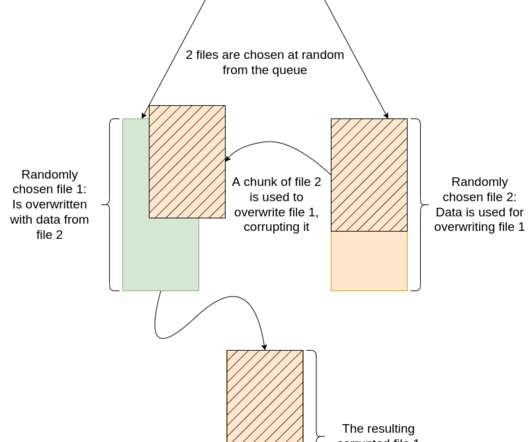
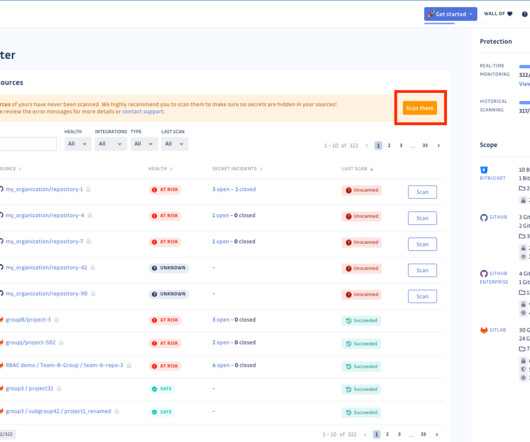
To accelerate the ransomware encryption process and make it harder to detect, cybercriminal groups have begun using a new technique: intermittent encryption. Intermittent encryption allows the ransomware encryption malware to encrypt files partially or only encrypt parts of the files. Others are automated.

eSecurity Planet
JULY 26, 2022
Even the most advanced and sophisticated security tools are failing to protect against ransomware and data exfiltration, according to a new report from data encryption vendor Titaniam. The organizations affected had solid cybersecurity measures, but nonetheless experienced significant data security failures.
The Security Ledger
JANUARY 14, 2022
Host Paul Roberts speaks with Marc Blackmer of ShardSecure about that company’s new approach to protecting data at rest, which relies on fragmenting and scattering data to make it impossible to steal. The post Spotlight: ShardSecure on Protecting Data At Rest Without Encryption appeared first on The Security Ledger with Paul F.

Thales Cloud Protection & Licensing
NOVEMBER 2, 2021
Quantum Resistant Encryption – Are You Ready? Over the past few months, a handful of Thales CPL clients have mentioned their concern regarding the future threat of quantum computing to their data security frameworks. Learn more about Thales solutions for quantum resistant encryption. Encryption. More About This Author >.

Thales Cloud Protection & Licensing
NOVEMBER 15, 2021
How encryption can help address Cloud misconfiguration. Cloud service providers (CSPs) try to make it simple and easy for their users to comply with data privacy regulations and mandates. The gateway into the database was Microsoft's Jupyter Notebook, which enabled data visualizations and customized views.

Data Breach Today
SEPTEMBER 25, 2020
Many Vendors of Illegal Drugs, Weapons, Hacking Tools Prefer Markets With so many cybercrime markets continuing to disappear, why haven't encrypted messaging apps stepped in to fill the gap? But encrypted apps have their own downsides.

Schneier on Security
NOVEMBER 1, 2022
It’s Iran’s turn to have its digital surveillance tools leaked : According to these internal documents, SIAM is a computer system that works behind the scenes of Iranian cellular networks, providing its operators a broad menu of remote commands to alter, disrupt, and monitor how customers use their phones.

The Last Watchdog
FEBRUARY 18, 2020
It was just a few short years ago that the tech sector, led by Google, Mozilla and Microsoft, commenced a big push to increase the use of HTTPS – and its underlying TLS authentication and encryption protocol. Related: Why Google’s HTTPS push is a good thing At the time, just 50 % of Internet traffic used encryption.

The Last Watchdog
SEPTEMBER 30, 2019
Homomorphic encryption has long been something of a Holy Grail in cryptography. Related: Post-quantum cryptography on the horizon For decades, some of our smartest mathematicians and computer scientists have struggled to derive a third way to keep data encrypted — not just the two classical ways, at rest and in transit.
eSecurity Planet
OCTOBER 18, 2021
This has given rise to a large number of open source security tools. However, the tools themselves vary considerably in scope, sophistication, and function. The editors of eSecurity Planet find the following 20 open source security tools to be particularly useful. The Best Open Source Security Tools. WhiteSource.

Security Affairs
NOVEMBER 8, 2023
As of July 2023, the FBI observed ransomware operators exploiting vulnerabilities in vendor-controlled remote access to casino servers, and companies that were compromised through legitimate system management tools to elevate network permissions. ” reported the PIN.

eSecurity Planet
APRIL 12, 2024
Data loss prevention (DLP) best practices are principles that help prevent intentional or unintentional data erasure. By following these guidelines, organizations can reduce the detrimental impact of data loss and quickly resume operations after an incident. Proofpoint’s 2024 data loss landscape report reveals 84.7%
eSecurity Planet
NOVEMBER 25, 2020
Encryption remains a mainstay of IT security technology, a critical tool for protecting sensitive data. We evaluate the top encryption solutions.
eSecurity Planet
OCTOBER 6, 2021
Successful assaults can lead to locked up data and systems, as well as stolen and leaked data, bringing chaos to the targeted companies. The malware encrypts files and spreads to the entire system to maximize damage, which forces companies to lock down the whole network to stop the propagation. Encryption is the Key.

Thales Cloud Protection & Licensing
JANUARY 13, 2021
Data Encryption Shields the Energy Sector Against Emerging Threats. According to a Siemens/Ponemon report , in 2019, 56% of gas, wind, water and solar utilities around the world experienced at least one cyberattack that caused a shutdown or loss of operational data. Wed, 01/13/2021 - 09:42. What the energy sector seeks.
Data Breach Today
OCTOBER 4, 2021
DSCI: Ransomware Alkhal Likely Spread Via Phishing, Malicious URLs The Data Security Council of India has issued an advisory about newly discovered ransomware Alkhal, which uses a strong encryption tool and has no known decryptor to recover lost data. The ransomware was likely discovered on Oct.

The Last Watchdog
MAY 3, 2021
Encryption agility is going to be essential as we move forward with digital transformation. All of the technical innovation cybersecurity vendors are churning out to deal with ever-expanding cyber risks, at the end of the day, come down to protecting encrypted data. Refer: The vital role of basic research.

Thales Cloud Protection & Licensing
MARCH 4, 2021
The Cloud Trust Paradox: Keeping Control of Data & Encryption Keys in the Cloud. With customers increasingly being less trusting of how companies store and process their data in the cloud, encrypting this data and controlling the encryption keys is essential for building trust. Thu, 03/04/2021 - 09:38.
Security Affairs
SEPTEMBER 26, 2022
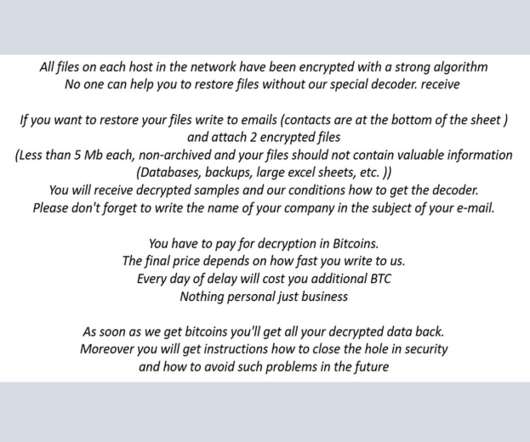
Ransomware operators switch to new extortion tactics by using the Exmatter malware and adding new data corruption functionality. The data extortion landscape is constantly evolving and threat actors are devising new extortion techniques, this is the case of threat actors using the Exmatter malware.
Thales Cloud Protection & Licensing
AUGUST 16, 2023
Enterprise Secrets Management Explained: Best Practices, Challenges, and Tool Selection madhav Thu, 08/17/2023 - 06:28 Whether hosted in the cloud or on-premises, modern applications and integrations have accelerated the need for digital secrets. This includes sensitive data such as passwords, encryption keys, APIs, tokens, and certificates.
eSecurity Planet
MAY 19, 2023
Application security tools and software solutions are designed to identify and mitigate vulnerabilities and threats in software applications. Their main purpose is to protect applications from unauthorized access, data breaches, and malicious attacks.

Security Affairs
FEBRUARY 19, 2024
The Cactus ransomware gang claims the theft of 1.5TB of data from the Energy management and industrial automation firm Schneider Electric. The Cactus ransomware group claims responsibility for pilfering 1.5TB of data from the Energy management and industrial automation giant Schneider Electric.

The Last Watchdog
JULY 30, 2018
One sliver of the $90 billion, or so, companies are expected to spend this year on cybersecurity products and services is an estimated $85 million they will shell out for encrypted flash drives. We discussed why encrypted flash drives have become established as a must-have portable business tool in the digital age.
Security Affairs
SEPTEMBER 9, 2022
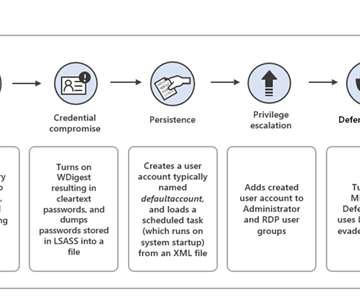
Iran-linked APT group DEV-0270 (aka Nemesis Kitten) is abusing the BitLocker Windows feature to encrypt victims’ devices. Microsoft Security Threat Intelligence researchers reported that Iran-linked APT group DEV-0270 ( Nemesis Kitten ) has been abusing the BitLocker Windows feature to encrypt victims’ devices.
Thales Cloud Protection & Licensing
OCTOBER 19, 2021
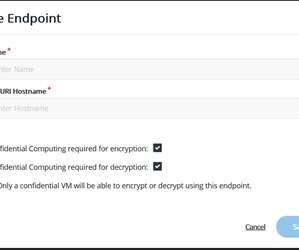
CipherTrust Data Security Platform now allows users to control encryption keys for data processed by Google Cloud’s Confidential Computing. The Thales partnership with Google Cloud takes a huge step forward with the announcement of Google Cloud ubiquitous data encryption. Tue, 10/19/2021 - 06:19.

The Last Watchdog
FEBRUARY 5, 2024
Even in the cloud era, Microsoft Exchange Server remains a staple business communications tool across the globe. Related: The need for robust data recovery policies. And this has material value for organizations concerned about data sovereignty.
Thales Cloud Protection & Licensing
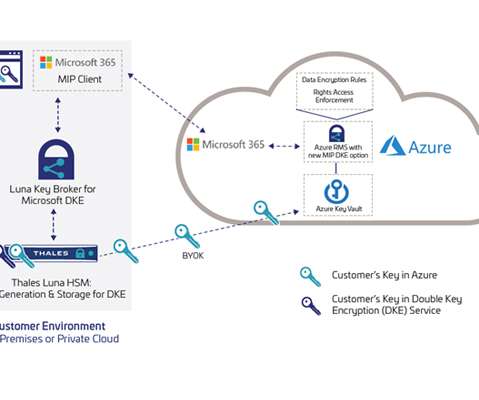
APRIL 1, 2021
Protecting Sensitive Data with Luna Key Broker for Microsoft Double Key Encryption. Today’s remote working environment relies heavily on the collaborative sharing of information, challenging organizations to maintain the security of confidential data and regulatory compliance while driving employee productivity.

Security Affairs
JANUARY 24, 2023
GoTo is notifying customers that its development environment was breached in November 2022, attackers stole customers’ backups and encryption key. ” reads the data breach notification. Now the investigation revaled that threat actors were able to access customers’ data. ” continues the notice.

eSecurity Planet
JUNE 24, 2021
The increasing mobility of data, as it ping-pongs between clouds, data centers and the edge, has made it an easier target of cybercrime groups, which has put a premium on the encryption of that data in recent years. The data is protected against cybercriminals as well as others who are not supposed to see it.
Krebs on Security
NOVEMBER 17, 2022
He’d been on the job less than six months, and because of the way his predecessor architected things, the company’s data backups also were encrypted by Zeppelin. “We’ve found someone who can crack the encryption.” Then came the unlikely call from an FBI agent. This is not an idle concern.
Security Affairs
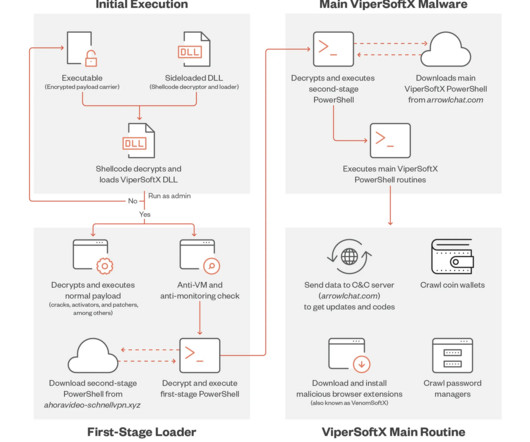
APRIL 29, 2023
xyz pic.twitter.com/VLhISark8Y — Goldwave (@OGoldwave) March 13, 2023 The variant employed in the campaign supports a more sophisticated encryption method of byte remapping and a monthly rotation of the C2 server. #ViperSoftX is back, doesn't look like much has changed. c2 arrowlchat[.]com ” concludes the report.
eSecurity Planet
OCTOBER 25, 2022
Symantec researchers are warning that a BlackByte ransomware affiliate has begun using a custom data exfiltration tool, Infostealer.Exbyte, to steal data from victims’ networks as part of their attacks. BlackByte Exfiltration Tool. Exfiltration to Replace Ransomware Encryption?
Security Affairs
FEBRUARY 12, 2024
Exploring the Risks: Unveiling 9 Potential Techniques Hackers Employ to Exploit Public Wi-Fi and Compromise Your Sensitive Data We’ve all used public Wi-Fi: it’s convenient, saves our data, and speeds up browsing. Look for the “https” in the website’s URL—it means there’s some level of encryption.

Data Breach Today
MAY 14, 2018
Exploitable Vulnerabilities Could Reveal Plaintext of Encrypted Emails European computer security researchers say they have discovered vulnerabilities that relate to two techniques used to encrypt emails: PGP and S/MIME. Security experts recommend all PGP users immediately delete or disable their PGP tools, pending a full fix.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content