Quantum Computing: A New Dawn for Encryption Vulnerabilities
Data Breach Today
MARCH 19, 2024
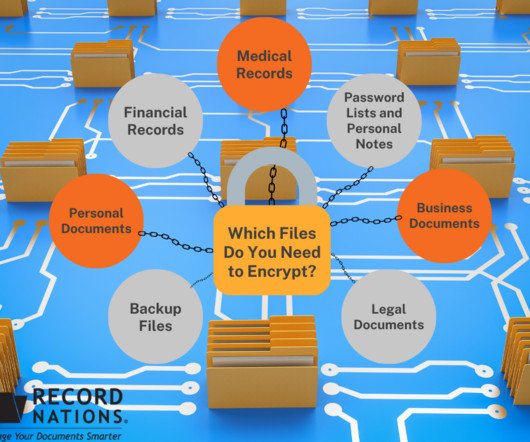
Expert Perspectives on Protecting Data and Developing Quantum-Safe Cryptography As quantum computing looms, experts emphasize the urgency of embracing quantum-safe strategies. They highlight the need for proactive measures to protect digital assets from future breaches, deliver long-term data security and ensure the integrity of encryption.










































Let's personalize your content