RedEnergy Stealer-as-a-Ransomware employed in attacks in the wild
Security Affairs
JULY 5, 2023
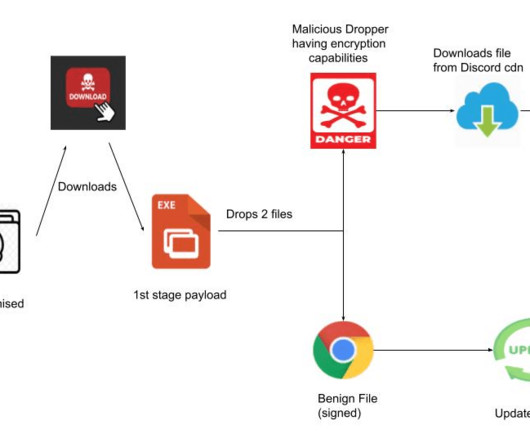
“The sample Stealer-as-a-Ransomware variant analyzed in this case study employs a deceptive FAKEUPDATES campaign to lure in its targets, tricking them into promptly updating their browsers. The malware communicates with the command and control servers through HTTPS. ” reads the analysis published by Zscaler.















Let's personalize your content