A Case Study - Db2 for z/OS High-Performance DBATs
Robert's Db2
JULY 31, 2020
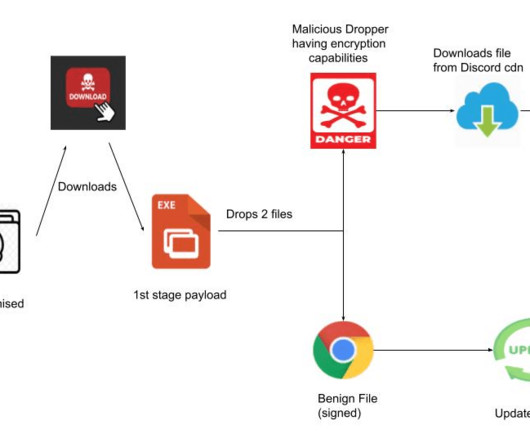
That implementation effort has involved a good bit of back-and-forth communication between myself and the Db2 administrator, and I saw that it makes for a good case study that touches on many of the issues associated with high-performance DBAT set-up, monitoring and usage. And there you have it.











































Let's personalize your content