Turn up the volume with Table Top Exercises
OpenText Information Management
JUNE 7, 2022
MITRE released a new edition of its book on “the way security operations is done”, 11 Strategies of a World-Class Cybersecurity Operations Center.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

OpenText Information Management
JUNE 7, 2022
MITRE released a new edition of its book on “the way security operations is done”, 11 Strategies of a World-Class Cybersecurity Operations Center.

Data Matters
MAY 5, 2020
First, as covered in an earlier posting , HHS took action to waive penalties and assure companies that it would exercise enforcement discretion with respect to the Privacy Rule’s application to telehealth services and certain limited communication activities related to COVID-19 treatment efforts.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

IT Governance
APRIL 27, 2018
This week, we discuss TSB’s chaotic system upgrade, a security flaw in electronic hotel locks and a major NATO cyber security exercise. Security researchers have discovered that millions of electronic door locks used in hotel rooms around the world are vulnerable to hacking. Here are this week’s stories.

Security Affairs
APRIL 30, 2023
Credit: ESA – European Space Agency The offensive cybersecurity team at Thales demonstrated how to take control of the ESA satellite, the is considered the world’s first ethical satellite hacking exercise. The exercise aims at assessing the resilience of satellites to cyber attacks. According to classified U.S.

Data Matters
AUGUST 10, 2023
Securities and Exchange Commission (SEC or Commission) proposed new rules for broker-dealers (Proposed Rule 15(1)-2) and investment advisers (Proposed Rule 211(h)(2)-4) on the use of predictive data analytics (PDA) and PDA-like technologies in any interactions with investors. On July 26, 2023, the U.S.

OpenText Information Management
OCTOBER 19, 2022
It’s important to exercise sound cybersecurity best practices to protect your organization’s sensitive and valuable information against outside hackers and cybercriminals that are always identifying new ways to get to your data. October is Cybersecurity Awareness Month.

IT Governance
FEBRUARY 9, 2021
If your marketing agency is under the impression that cyber security is strictly an IT issue, you should think again. Effective security is a company-wide commitment, and marketers play one of the most crucial roles. The system helps organisations manage, monitor and improve their security practices in one place.

OpenText Information Management
MARCH 28, 2024
Environmental Protection Agency and National Security Agency have requested that each U.S. DNS Exfil, SCADA controls, DGA), but also need the additional layer of security that may be missed by using only endpoint protection (e.g. State carry out comprehensive assessments of their cybersecurity services and practices.

Security Affairs
MAY 17, 2023
The organization is located in Tallinn, Estonia, and conducts research, training, and exercises in the field of cyber defence, and provides a platform for sharing expertise and best practices. Our goal is to foster increased cooperation and reap the benefits of this large-scale coalition through research, training, and exercises.”

Security Affairs
SEPTEMBER 17, 2023
CardX recommends that customers keep track of transactions involving their accounts and exercise caution to avoid any potential fraud. CardX has upgraded its systems and implemented additional security measures to prevent further information leaks. CardX is a company in the SCB X Group in Thailand.

Hunton Privacy
AUGUST 9, 2017
On August 4, 2017, the FTC published the third blog post in its “Stick with Security” series. As we previously reported , the FTC will publish an entry every Friday for the next few months focusing on each of the 10 principles outlined in its Start with Security Guide for Businesses.

Security Affairs
MAY 28, 2022
“Dearlove said that the emails captured a “legitimate lobbying exercise which, seen through this antagonistic optic, is now subject to distortion.”” ”” Security Affairs is one of the finalists for the best European Cybersecurity Blogger Awards 2022 – VOTE FOR YOUR WINNERS. Pierluigi Paganini.

Hunton Privacy
OCTOBER 3, 2017
On September 29, 2017, the Federal Trade Commission published the eleventh blog post in its “Stick with Security” series. As previously reported , the FTC will publish an entry every Friday for the next few months focusing on each of the 10 principles outlined in its Start with Security Guide for Businesses.

Troy Hunt
AUGUST 11, 2023
😊 The new subscription model launched this week and as many of you know from your own past experiences, pushing major new code live is always a bit of a nail-biting exercise. I expect I'll blog that this coming week and probably quietly slip out the documentation on the 2 new endpoints in advance.

AIIM
APRIL 16, 2020
But, as you start your social distancing/remote working, there are certain strict and important practices that every organization will have to exercise. Are you ready to learn the best security practices for remote working that can be used both by organizations and employees for maintaining ethics and productivity? Let’s get started!

Lenny Zeltser
AUGUST 23, 2023
Start by critically reviewing how you’ll spend the security funds; this involves broadening your perspective beyond security. Try a Zero-Based Approach to Security Spending Regardless of the formal process your company uses for budgeting, review your security expenses using an approach known as zero-based budgeting.

IT Governance
APRIL 4, 2024
A Springboard to Career Success CISM® (Certified Information Security Manager) is a globally recognised qualification that provides a good understanding of IT security with a management flavour. How is CISM different from general information security certifications? It’s not just technical training – it’s management training.

IT Governance
FEBRUARY 25, 2019
A version of this blog was originally published on 8 December 2017. There has never been a better time to get into cyber security, with growing demand for experts promising increased salaries and job opportunities. In this blog, we provide tips for getting your cyber security career started no matter your background.
Security Affairs
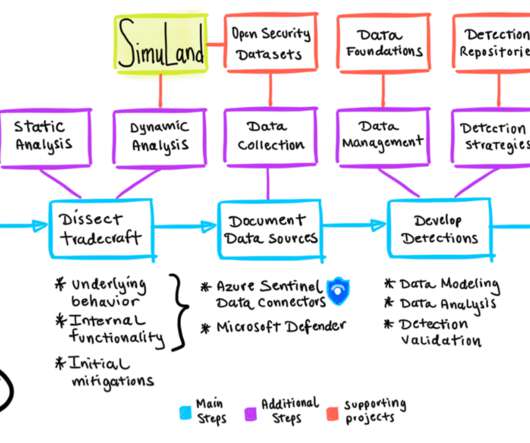
MAY 20, 2021
“These lab environments will provide use cases from a variety of data sources including telemetry from Microsoft 365 Defender security products, Azure Defender and other integrated data sources through Azure Sentinel data connectors.” ” reads a blog post published by Microsoft. Pierluigi Paganini.

IT Governance
DECEMBER 20, 2022
Although there have still been a few surprises, with the death of Queen Elizabeth II and blazing heatwaves across the UK to name but two, it was a familiar year in the cyber security landscape. Google , Clearview AI , and Meta all receives hefty penalties in 2022, demonstrating the continued important of effective information security.
Security Affairs
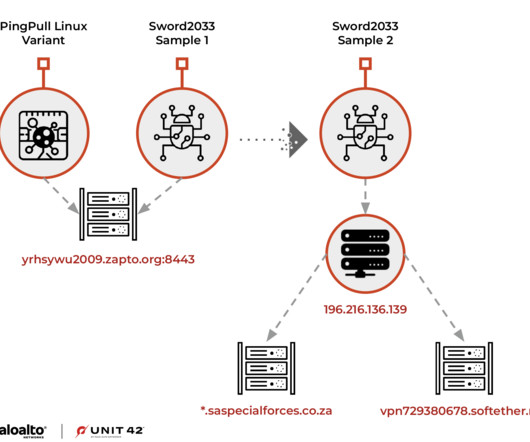
APRIL 26, 2023
The Alloy Taurus APT group targeted South Africa because in February 2023, the African state joined Russia and China to participate in combined naval exercises. Alloy Taurus is known for leveraging the SoftEther VPN service to facilitate access and maintain persistence to their targeted network.

Data Matters
FEBRUARY 6, 2019
The stolen information allegedly included names and identifying information, hashed passwords, security questions and answers, family information, Social Security numbers, lab results, health insurance information, doctor’s names, and medical conditions, among other things.

IT Governance
OCTOBER 13, 2021
Whatever your level of knowledge and expertise, following our certification path will help you develop your career with the knowledge and qualifications you need to practise Azure administration and security management. . Please note that this two-day course includes practical, hands-on lab exercises. . The course covers: .

Thales Cloud Protection & Licensing
SEPTEMBER 12, 2019
Just a couple of months after that, World Rugby itself announced that one of its training websites had suffered a security breach that exposed subscribers’ account information. That’s why it announced it would pursue two measures designed to strengthen its national digital security posture ahead of these sporting events.

Troy Hunt
APRIL 10, 2020
(this was just super good fun, it's now all hooked up to Alexa too) Pwned Passwords is getting bigger and bigger (more than half a billion queries in a month now) I hate spam and I hate being asked to link to spammy articles (but I love the outcome of this blog post!) Download the guide by Duo Security.

Security Affairs
MAY 12, 2022
. “The CSA—created in response to reports of increased activity against MSPs and their customers—provides specific guidance for both MSPs and customers aimed at enabling transparent discussions on securing sensitive data.” Improve security of vulnerable devices. Develop and exercise incident response and recovery plans.
Security Affairs
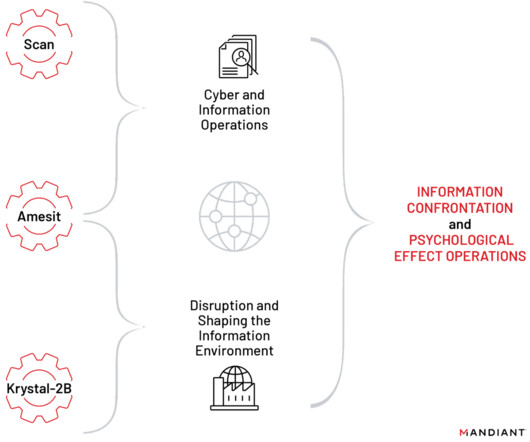
APRIL 2, 2023
These projects include tools, training programs, and a red team platform for exercising various types of offensive cyber operations, including cyber espionage, IO, and operational technology (OT) attacks.” ” reads the report published by Mandiant.

Security Affairs
MAY 14, 2022
The Italian police is investigating the attack, while the National Computer Security Incident Response Team (CSIRT) confirmed that the websites were hit with DDoS attacks. Our Legion conducts military cyber exercises in your countries in order to improve their skills. To nominate, please visit:? Pierluigi Paganini.
Information Governance Perspectives
APRIL 13, 2023
So, before you walk a virtual mile in the shoes of innovative business leaders profiled in a book like Tomorrow’s Jobs Today , practice this simple exercise first. The security that comes with the job. The post 6 Motivators Every Job Seeker Must Consider appeared first on The Bastards Blog. The money you hope to earn.
IT Governance
APRIL 15, 2020
The video conferencing platform Zoom has been heavily criticised in recent weeks , amid a series of allegations related to its inadequate cyber security and privacy measures. It’s worth emphasising, then, that for all of Zoom’s security faults, the blame for this incident lies with users rather than the platform. Cyber attacks.

The Last Watchdog
AUGUST 23, 2021
With many employees now working remotely, securing company data isn’t as straightforward as it used to be. International workforces can be an excellent way to find top talent, but they can introduce unique security risks. Countries have different data security laws, and these can get in the way of one another.

Thales Cloud Protection & Licensing
APRIL 24, 2019
Ensuring that systems behave only how a designer intends is a central aspect of security. A security-enforcing system will take the context of available information measured against policy to determine whether an operation should be permitted or denied. MBSE and security engineering. Model-Based Systems Engineering.

Data Matters
SEPTEMBER 30, 2020
national security law did not provide equivalent privacy protections to those available in the EU. national security law protects EU personal data. Given the detail set forth in the Paper, and the CJEU’s silence regarding any actual comparison of the relative national security safeguards of the U.S. agencies is compelling.

The Last Watchdog
APRIL 11, 2022
However, starting with a strong security foundation goes a long way. A security program built on a strong foundation will be strong, a security program built on a shaky foundation will be shaky. Having a security tool such as endpoint protection isn’t enough.

IT Governance
APRIL 20, 2020
With the coronavirus pandemic keeping us stuck inside and struggling to find ways to remain productive, now might be the perfect time to take an online cyber security training course. Let’s take a look at five of the best online courses for cyber security. Certified Cyber Security Foundation Training Course.
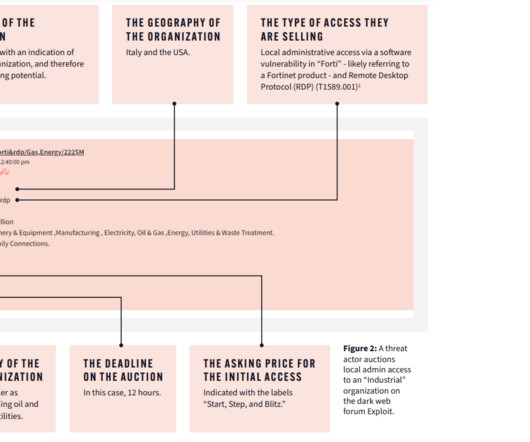
Security Affairs
MAY 17, 2023
Dark web intelligence is a fantastic resource for informing an organization’s security posture, helping the security team spot early indicators of attack and feeding their threat models. The threat actors offered detailed instructions on how to exploit known vulnerabilities in Internet-facing ICS systems. We are in the final!

IBM Big Data Hub
AUGUST 16, 2023
A red team engagement gives your blue team a chance to more accurately assess your security program’s effectiveness and make improvements. Find out about the benefits of red teaming, the differences between red and blue teams and what a purple team is in my previous blog post, “ Red teaming 101: What is red teaming?

Troy Hunt
JUNE 11, 2021
I'm writing up a much more extensive blog post on this, suffice to say it's a complete mess and all of the suggestions I've had have been well-intentioned, but infeasible for various reasons. References Trying to get local control of Tuya lights is an exercise in absolute futility (read the thread to feel my pain ??)
Security Affairs
APRIL 28, 2023
OpenAI explained that it had expanded the information to European users and non-users, that it had amended and clarified several mechanisms and deployed amenable solutions to enable users and non-users to exercise their rights.”

Data Matters
JANUARY 28, 2022
The advisory was promptly endorsed by the National Cyber Security Centre, a division of Government Communications Headquarters (“GCHQ”), a UK intelligence agency. Create, Maintain, and Exercise a Cyber Incident Response, Resilience, and Continuity of Operations Plan. The post U.S.

IT Governance
JUNE 22, 2023
This data breach is the latest in a series of security concerns regarding machine learning tools. Does ChatGPT pose a cyber security risk? Cyber security experts currently sit somewhere between those parties. Indeed, these issues mirror the industry’s general concern about the way people view cyber security technology.

Data Protection Report
JUNE 17, 2020
The opinion suggested that parties using the SCCs need to make an assessment of whether the national security, communication and surveillance laws of the country of the data importer are “essentially equivalent” to those in the EU, i.e. they respects privacy rights and freedoms, provide effective remedies, etc.

IBM Big Data Hub
FEBRUARY 16, 2024
Breach and Attack Simulation (BAS) is an automated and continuous software-based approach to offensive security. Similar to other forms of security validation such as red teaming and penetration testing , BAS complements more traditional security tools by simulating cyberattacks to test security controls and provide actionable insights.
IT Governance
APRIL 1, 2020
That means ensuring that you remain productive and – just as important – safe, both in terms of your organisation’s security posture and your mental wellbeing. In this blog, we discuss the importance of remaining calm in these stressful circumstances. How your mental health affects your organisation’s security hygiene.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content