Analysis: Self-Driving Tractors at Risk of Being Hacked
Data Breach Today
AUGUST 13, 2021
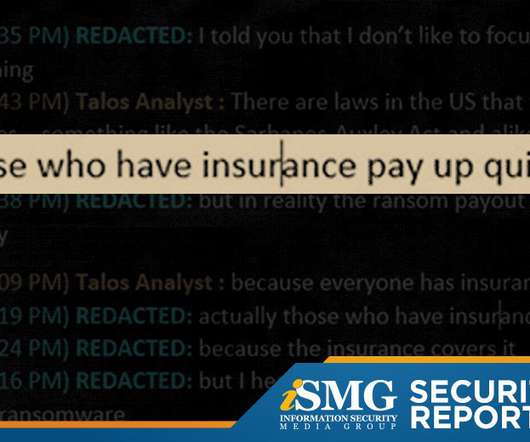
This edition of the ISMG Security Report offers an analysis of how tractors manufactured by John Deere are at risk of being hacked. Also featured: a description of the infrastructure bill passed by the Senate that would boost cybersecurity funding and an update on the reboot of the AlphaBay darknet market.














































Let's personalize your content