4 ways generative AI addresses manufacturing challenges
IBM Big Data Hub
APRIL 15, 2024
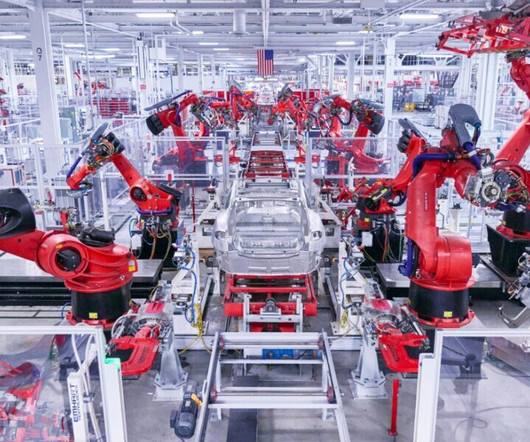
The manufacturing industry is in an unenviable position. Manufacturers are being called to reduce their carbon footprint, adopt circular economy practices and become more eco-friendly in general. And manufacturers face pressure to constantly innovate while ensuring stability and safety.




































Let's personalize your content