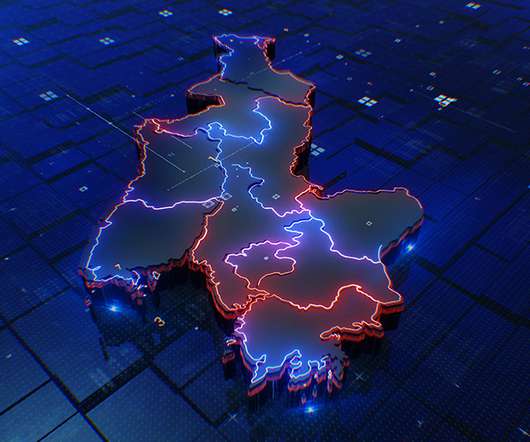
Ransomware Profits Dip as Fewer Victims Pay Extortion
Data Breach Today
JANUARY 23, 2023
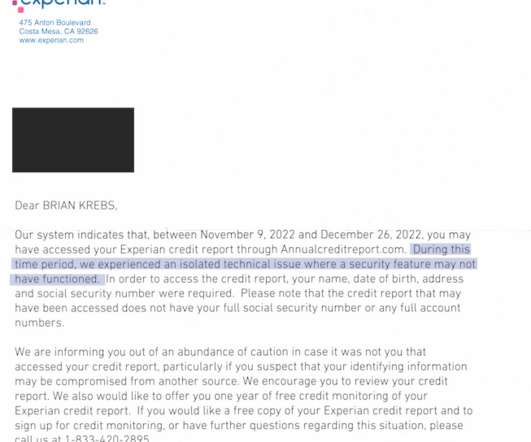
As Funding From Ransoms Goes Down, Gangs Embrace Re-Extortion, Researchers Warn Bad news for ransomware groups: Experts find it's getting tougher to earn a crypto-locking payday at the expense of others. The bad guys can blame a move by law enforcement to better support victims, and more organizations having robust defenses in place, which makes them tougher to take down.

































Let's personalize your content