InfoGovCon 2016 Promo Video
JKevinParker
JULY 20, 2016
Check out the new promo video for InfoGovCon 2016 ! I'm excited to be one of the speakers for this exciting event. You should come! Learn more at: www.InfoGovCon.com.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

JKevinParker
JULY 20, 2016
Check out the new promo video for InfoGovCon 2016 ! I'm excited to be one of the speakers for this exciting event. You should come! Learn more at: www.InfoGovCon.com.

Hunton Privacy
JULY 8, 2019
The updates aim to answer questions about data breaches received by the Dutch DPA from organizations since 2016. In particular, the Dutch DPA expanded its Q&As section on the obligation to report data breaches and on how companies must react in the event of a data breach.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Security Affairs
DECEMBER 27, 2023
Key events include the European Parliament elections in June, the U.S. The 2016 US presidential elections and Brexit have demonstrated how, through the manipulation of information, it is possible to influence the perception of entire populations on issues of interest to the community.

eDiscovery Daily
FEBRUARY 18, 2019
O’Hara denied the plaintiff’s motion for sanctions based on the defendant’s alleged spoliation of a surveillance video that shows an altercation between the plaintiff and her supervisor, stating that “plaintiff has failed to meet the requirements of Fed. Case Background. The plaintiff subsequently filed the suit in July 2017.

Preservica
SEPTEMBER 20, 2016
The ICA is a truly international organisation, and this year held their Congress event in Seoul, South Korea. The event attracts a high number of senior practitioners including head archivists with extensive experience.
Security Affairs
SEPTEMBER 30, 2020
Security experts Simon Zuckerbraun from Zero Day Initiative published technical details on how to exploit the Microsoft Exchange CVE-2020-0688 along with a video PoC. Researchers from Rapid7 reported that 61 percent of Exchange 2010, 2013, 2016 and 2019 servers are still vulnerable to the vulnerability.

The Texas Record
SEPTEMBER 26, 2018
Whether you prefer learning at a live event or from your desk, there are resources available for you, your colleagues, and your agency staff to increase your records management and information technology knowledge. The DIR Statewide Data Program overview offers ten short video segments based on the Data Management Book of Knowledge.
ARMA International
APRIL 18, 2022
resumes, personnel files, video/call recordings). This may also include the use of event codes that are subjective or difficult to define in practice or retention periods that are correct in theory but impossible to implement. 2016/679 (EU, April 27). 2016/679, Art. 2016/679 (EU, April 27). Conclusion. 2 DLA Piper.

Security Affairs
SEPTEMBER 10, 2021
Run event-driven applications, quickly deploy from your container development pipelines, and run data processing and build jobs. rc2, it was released in 2016, and was affected by at least two container escape issues. Palo Alto researchers discovered that ACI use RunC, a lightweight, portable container runtime.
Security Affairs
NOVEMBER 28, 2021
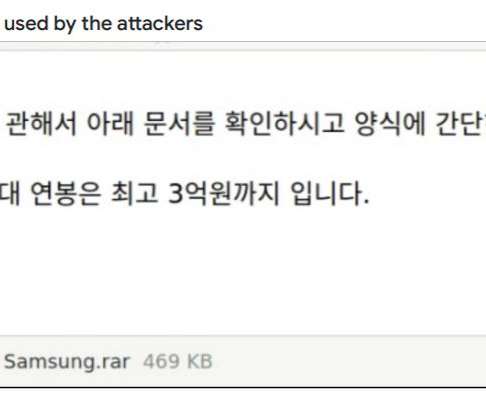
The group is considered responsible for the massive WannaCry ransomware attack, a string of SWIFT attacks in 2016, and the Sony Pictures hack. io ), to share videos of their claimed exploits, and for amplifying and retweeting posts from other accounts under their control.
Security Affairs
JANUARY 29, 2021
The group is considered responsible for the massive WannaCry ransomware attack, a string of SWIFT attacks in 2016, and the Sony Pictures hack. io ), to share videos of their claimed exploits, and for amplifying and retweeting posts from other accounts under their control.

eSecurity Planet
APRIL 1, 2024
The fix: Apply the emergency fixes issued by Microsoft for: Windows Server 2022 Windows Server 2019 Windows Server 2016 Windows Server 2012 R2 Attackers Actively Exploit Fortinet Enterprise Management Server SQLi Flaw Type of vulnerability: SQL injection (SQLi) flaw. The fix: Cisco recommends prompt application of patches.

eDiscovery Daily
SEPTEMBER 9, 2019
It will also be instructed that if it determines that the Police Department destroyed evidence and did so with the intent to deprive Woods of the use of the video footage, it may infer that the footage would have been favorable to Woods. CV-17-08038-PCT-GMS (D. 14, 2019) , Arizona Chief District Judge G. Case Background.

Security Affairs
JULY 25, 2019
STC) has been sanctioned for interfering with the 2016 U.S. Monokle has been used in highly targeted attacks at least since March 2016, it supports a wide range of spying functionalities and implements advanced data exfiltration techniques. Petersburg, Russia-based company, Special Technology Centre, Ltd. ( Presidential election.

Hunton Privacy
DECEMBER 5, 2016
On November 30, 2016, the FTC released a staff summary (the “Summary”) of a public workshop called Putting Disclosures to the Test. The workshop, which was held on September 15, 2016, examined ways of testing and evaluating company disclosures regarding advertising claims and privacy practices.

Hunton Privacy
OCTOBER 11, 2016
On October 3, 2016, the Texas Attorney General announced a $30,000 settlement with mobile app developer Juxta Labs, Inc. Juxta”) stemming from allegations that the company violated Texas consumer protection law by engaging in false, deceptive or misleading acts or practices regarding the collection of personal information from children.

ForAllSecure
JUNE 2, 2021
Some hackers live stream events. That’s George Hotz, aka GeoHot, who played for the CTF team Plaid Parliament of Pawning or PPP in 2016, but previously, at age 17, is much better known for being the very first person to jailbreak his iPhone so that he could use any carrier he wanted. Massive numbers.

ForAllSecure
JUNE 2, 2021
Some hackers live stream events. That’s George Hotz, aka GeoHot, who played for the CTF team Plaid Parliament of Pawning or PPP in 2016, but previously, at age 17, is much better known for being the very first person to jailbreak his iPhone so that he could use any carrier he wanted. Massive numbers.

Data Protection Report
FEBRUARY 13, 2024
The FTC’s complaint states: “From 2016 to the present, about 100 million unique devices sent Respondent location data each year.” (Complaint ¶ 5 (emphasis in original)) InMarket would share advertising revenue with developers that incorporated the InMarket SDK into their apps. We have twice covered the consumer class action, here and here.)

ARMA International
SEPTEMBER 22, 2021
Implied herein is a cloud computing model that ARMA (2016) defines as “A model for enabling ubiquitous, convenient, on-demand network access to a shared pool of configurable computing resources (e.g., COLD is a “technology that records and then stores computer-generated data onto optical disks for online access” (ARMA 2016, p 10).

ARMA International
NOVEMBER 15, 2019
xi] The term “information” covers any phenomena, including physical or digital objects, intangible knowledge, events, and nearly everything that could be considered as informative. Berlin: Springer, 2016. New York: Arcade Publishing, 2016. Guillory, John. “The Memo and Modernity.” ” Critical Inquiry 31, no.

ForAllSecure
AUGUST 21, 2020
DARPA’s Cyber Grand Challenge in 2016 showed the world what's coming -- autonomous adversaries -- and raised serious questions. Imagine a gigantic eSports event where all the contestants are machines. It’s important to stress that CGC was a significant event in security. Pretty cool, eh?

Troy Hunt
NOVEMBER 25, 2020
Fortunately, that didn't include driving functions, but it did include the ability to remotely manage the climate control and as you can see in the video embedded in that post, I warmed things up for my mate Scott Helme from the other side of the world whilst he sat there on a cold, damp, English night.

ForAllSecure
AUGUST 21, 2020
DARPA’s Cyber Grand Challenge in 2016 showed the world what's coming -- autonomous adversaries -- and raised serious questions. Imagine a gigantic eSports event where all the contestants are machines. It’s important to stress that CGC was a significant event in security. Pretty cool, eh?

ForAllSecure
AUGUST 22, 2020
DARPA’s Cyber Grand Challenge in 2016 showed the world what's coming -- autonomous adversaries -- and raised serious questions. Imagine a gigantic eSports event where all the contestants are machines. It’s important to stress that CGC was a significant event in security. Pretty cool, eh?

ForAllSecure
FEBRUARY 22, 2023
And DARPA made the event interesting. But also like vector graphics, like video games, there's, you know that so we were doing Capture the Flag events and building hackable video games. It's like people who speed run video games versus just play it. Machines, not humans, playing capture the flag.

Architect Security
SEPTEMBER 24, 2020
They have easy access to social media messages, as well as social media photo and video footage and its associated metadata, and data downloaded from confiscated phones. They matched his DNA from their database to DNA extracted from a cigarette butt he left at the scene of the protest in 2016. Smith asked.

ForAllSecure
MAY 24, 2016
Just about every employee in our company has been involved in Capture the Flag exercises for the past several years, and we have been hosting these online events for our customers for about 3 years now. Rapid Fire is a special event we started hosting at our own in-person CTFs in 2014. Rapid Fire event at Cambridge 2 Cambridge.

JKevinParker
FEBRUARY 2, 2014
Project Policy 0x010085EC78BE64F9478AAE3ED069093B9963 Event Cancelled EventCanceled b8bbe503-bb22-4237-8d9e-0587756a2176. Project Policy 0x010085EC78BE64F9478AAE3ED069093B9963 Event Type EventType 5d1d4e76-091a-4e03-ae83-6a59847731c0. Project Policy 0x010085EC78BE64F9478AAE3ED069093B9963 UID UID 63055d04-01b5-48f3-9e1e-e564e7c6b23b.

Data Protection Report
NOVEMBER 3, 2017
Slightly over one year ago, several major distributed denial-of-service (“DDoS”) attacks took place, including a major event affecting the domain name service provider Dyn , which caused outages and slowness for a number of popular sites, including Amazon, Netflix, Reddit, SoundCloud, Spotify, and Twitter.

Troy Hunt
JANUARY 15, 2021
A little bit of a change of pace this week with the video being solely on the events unfolding around removing content, people and even entire platforms from the internet. It also raises some fascinating engineering challenges; could Parler have survived by building out their own physical infrastructure?

eSecurity Planet
MARCH 25, 2022
Between 2016 and 2018, the malware strain SamSam made brute force RDP attacks an integral part of its attacks on several public organizations. Additional security features include privileged password vaulting, cloud, and virtual infrastructure security, and integrations with existing security information and event managers (SIEM).
Krebs on Security
MARCH 1, 2021
One of those is Video Downloader Plus, which at one point claimed nearly 1.4 In 2016, hackers suspected of working for Russian state security services compromised databases for election systems in Arizona and Illinois. million active users. “ Hosting Solution Ltd. Doing so is almost always a high-risk proposition.

eDiscovery Daily
MARCH 15, 2018
E-discovery luminary and recipient of the Masters Conference Educator of the Year 2016, Mary provides ACEDS and its membership more than a decade of strong credibility and sound leadership within the e-discovery community. Mary is the Executive Director of the Association of Certified eDiscovery Specialists (ACEDS).

ForAllSecure
AUGUST 2, 2022
Vamosi: DEF CON turns 30 This year what began simply as a going away party for a coworker has since evolved over the decades into an annual summer tradition for InfoSec leaders in Las Vegas, which now includes other events such as besides Las Vegas, Diana is known as hackers summer camp. is or what it controls. interact with it.

ForAllSecure
SEPTEMBER 10, 2021
They began competing at DEF CON CTF, in 2010, and won first place in 2013 2014 2016 2017 and 2019. That's something that's a bit unique, there's typically a video game component with every competition. PPP competes internationally in many of the top competitions against many of the top competitors. We've also gamified it.

Security Affairs
MARCH 12, 2019
When the app is running, it shows an Apex Legends video and, then, the application prompts the user to press the “OK” button in order to verify the EA Mobile Account. net” there is a well-known malicious site, active since 2016, and related to a huge phishing network, in which also some URLs related to fake MS Office pages are present.
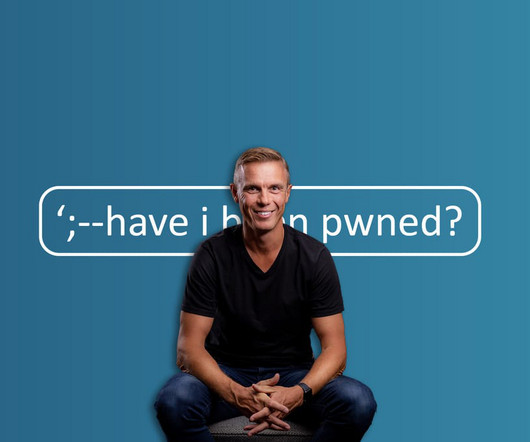
Troy Hunt
DECEMBER 3, 2023
These are often mainstream news events and what reporters often want to impart to people is along the lines of "Here's what you should do if you've been impacted", which often boils down to checking HIBP. How does the little site with the weird name end up in the press? And then ensured could never happen again.

Troy Hunt
JANUARY 10, 2018
million records on US consumers (this started a series events which ultimately led to me testifying in front of Congress ), South Africa had data on everyone living in the country (and a bunch of deceased folks as well) leaked by a sloppy real estate agent and data from Australia's Medicare system was being sold to anyone able to come up with $30.

Troy Hunt
MARCH 21, 2018
I very consciously avoided talking about it publicly at the time (largely because I didn't want to draw attention to it), but particularly around late 2016 and very early 2017, I was quite concerned with the broader genre that is data breach search services. The Industry Cleaned Up a Lot in 2017. in August last year.

eSecurity Planet
DECEMBER 19, 2023
As 2023 draws to an end and cybersecurity budgeting is nearly complete, it helps to consider the year’s events and try to predict next year’s trends. This will include synthetic written, spoken, and potentially even image or video content. Social media will become even more of a cesspool of AI and human-created garbage.”

The Security Ledger
AUGUST 16, 2019
The Mirai Botnet caught the world’s attention back in 2016 as the first, high profile IoT botnet. Sarah was presenting the CITL’s findings at an event sponsored by the Hewlett Foundation. On Firmware Security: Nobody’s Trying. Since then, attacks on Internet of Things devices have grown rapidly.

ARMA International
SEPTEMBER 27, 2021
Latson 2014) Unfortunately, the events unfolded almost exactly like the scenario in Situation Number 21. In 2016 the term “content services” entered management’s vernacular when Gartner redefined ECM to focus on CS applications, platforms, and components (Shegda, et al. Therefore, the risk did not seem to matter. Retrieved June 2021.

ForAllSecure
AUGUST 10, 2021
Vamosi: In 2016 I took a two day car hacking training session at BlackHat USA in Las Vegas. They had a reporter in the driver's seat on a Missouri interstate during rush hour, and captured on video how the researchers remotely turned off the brake system. This interview was actually recorded just before that event.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?


Let's personalize your content