A Case Study - Db2 for z/OS High-Performance DBATs
Robert's Db2
JULY 31, 2020
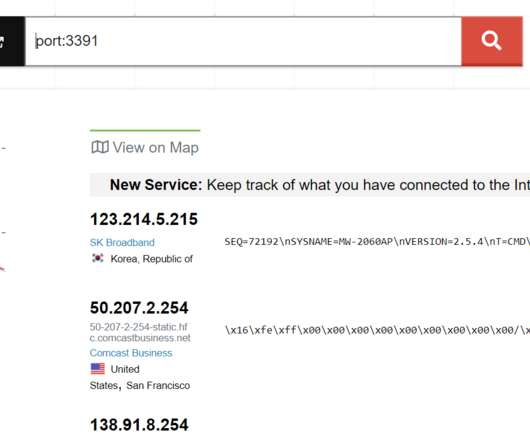
Over the years, I have posted several entries to this blog that have covered various aspects of Db2 for z/OS high-performance DBATs (examples are entries posted in 2016 and 2013 ). Accordingly, I decided to use this case study as the basis for a blog entry. And there you have it.

































Let's personalize your content