Google Stored G Suite Passwords in Plaintext Since 2005
Threatpost
MAY 22, 2019
Google said it had stored G Suite enterprise users' passwords in plain text since 2005 marking a giant security faux pas.
This site uses cookies to improve your experience. By viewing our content, you are accepting the use of cookies. To help us insure we adhere to various privacy regulations, please select your country/region of residence. If you do not select a country we will assume you are from the United States. View our privacy policy and terms of use.

Data Breach Today
FEBRUARY 9, 2023
CEO Change Marks First Time Since 2005 Someone Other Than Udi Mokady Is In Charge CyberArk will promote Matt Cohen, 47, to CEO on April 3.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.

WIRED Threat Level
MAY 21, 2019
On the heels of embarrassing disclosures from Facebook and Twitter, Google reveals its own password bugs—one of which lasted 14 years.

John Battelle's Searchblog
FEBRUARY 9, 2024
In my 2005 book , I imagined search evolving into what at that point was confined to science fiction: Search is a catalyst in promising attempts at cracking one mankind’s most intractable problems: the creation of artificial intelligence. And if Google decides to proactively drive that shift, it’ll come that much quicker.

Archives Blogs
OCTOBER 18, 2017
We are pleased to announce that after a significant transfer of records from the Revenue Services Department, the Archives can now make available property tax records up to 2005. 1978-1990 and 1992-2005: Property tax statements: series COV-S289. Map of assessment wards in the Municipality of Point Grey, with proposed changes, ~1927.

eSecurity Planet
FEBRUARY 10, 2022
Gartner first coined the term SIEM in 2005 to combine the technologies of security event management (SEM) and security information management (SIM). Gartner first coined the term SIEM in 2005 to combine the technologies of security event management (SEM) and security information management (SIM). What is a SIEM? How to Use a SIEM.

ChiefTech
MAY 23, 2012
I wrote this in June 2005. The history of intranets is one of a slow burn of adoption (or innovation, if you like). But the pace of technology change is increasing , email is being challenged. is it time now to dust off the intranet imperative and think about about where we go next? What exactly is an intranet?

Data Breach Today
NOVEMBER 15, 2017
The Final FFIEC Guidance has been issued and its main intent is to reinforce the 2005 Guidance's risk management framework and update the Agencies' expectations regarding customer authentication, layered security, or other controls in the increasingly hostile online environment.

Krebs on Security
JUNE 22, 2022
Stanx said he was a longtime member of several major forums, including the Russian hacker forum Antichat (since 2005), and the Russian crime forum Exploit (since April 2013). In an early post to Antichat in January 2005, Stanx disclosed that he is from Omsk , a large city in the Siberian region of Russia. info , allproxy[.]info

Unwritten Record
MARCH 15, 2024
Beginning with the 2005 session, the Court implemented a digital audio recording system, and began transferring digital audio files to NARA for preservation and public access. 412_DSP_WashingtonDC_018_8x10, [link] Today’s post was written by Dan Rooney, Director of NARA’s Special Media Records Division.

Krebs on Security
MAY 4, 2023
Launched in 2005, Try2Check soon was processing more than a million card-checking transactions per month — charging 20 cents per transaction. ” In February 2005, Nordex posted to Mazafaka that he was in the market for hacked bank accounts, and offered 50 percent of the take. Denis Kulkov, a.k.a. Image: USDOJ.
Krebs on Security
NOVEMBER 8, 2020
In 2005, AOL won a $12.8 Hawke had reportedly bragged about the money he earned from spam, but told friends he didn’t trust banks and decided to convert his earnings into gold and platinum bars. That sparked rumors that he had possibly buried his ill-gotten gains on his parents’ Massachusetts property.
Security Affairs
NOVEMBER 24, 2022
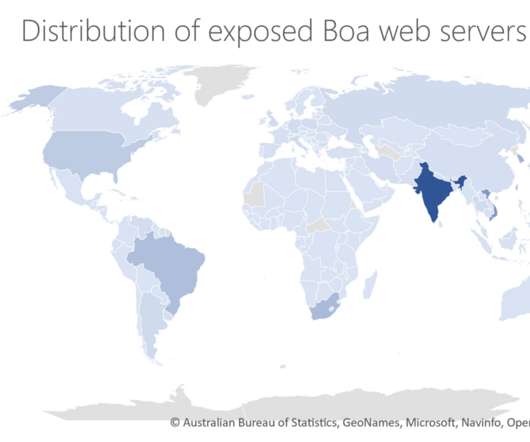
The experts pointed out that Boa has been discontinued since 2005. ” Microsoft experts explained that despite Boa being discontinued in 2005, many vendors across a variety of IoT devices and popular software development kits (SDKs) continue to use it. ” reads the report published by Microsoft. ” concludes the report.

Security Affairs
NOVEMBER 27, 2020
The hackers accessed company file servers that contained information about current and former employees from 2005 to 2020 and their beneficiaries and dependents. Canon finally confirmed that it has suffered a ransomware attack in early August that resulted in the theft of data from its servers. The gang has published a 2.2

Security Affairs
JULY 30, 2019
The security breach data breach took place on March 22nd and 23rd, the hacker accessed information of customers who had applied for a credit card between 2005 and 2019. . “Capital One quickly alerted law enforcement to the data theft — allowing the FBI to trace the intrusion,” said U.S. Attorney Moran. “I Pierluigi Paganini.
Krebs on Security
JANUARY 8, 2024
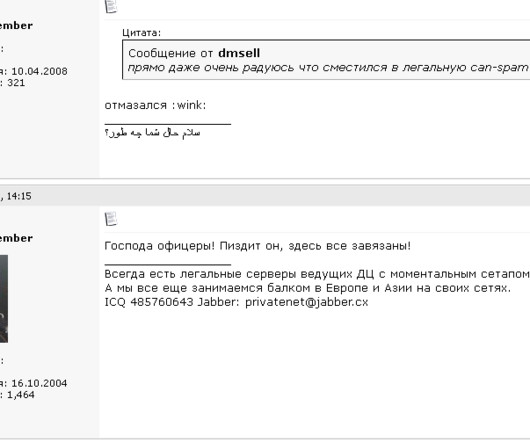
From January 2005 to April 2013, there were two primary administrators of the cybercrime forum Spamdot (a.k.a From one of his ads in 2005: Domains For Projects Advertised By Spam I can register bulletproof domains for sites and projects advertised by spam(of course they must be legal). w s, icamis[.]ru ru , and icamis[.]biz.
Krebs on Security
SEPTEMBER 1, 2021
An ad circa 2005 for A311 Death, a powerful banking trojan authored by “Corpse,” the administrator of the early Russian hacking clique Prodexteam. But roughly two weeks ago, VIP72’s online storefront — which ironically enough has remained at the same U.S.-based The domain Vip72[.]org
Krebs on Security
JUNE 28, 2022
ru’s original WHOIS records, which shows it was assigned in 2005 to a “private person” who used the email address lycefer@gmail.com. ru)was registered in 2005 to two men, one of whom was named Dmitry Sergeevich Starovikov. But on Dec. AWM Proxy’s online storefront disappeared that same day. and starovikov[.]com.

DXC Technology
APRIL 12, 2020
2005????????10???NIST???????????????????????????????????????????????????ICAS??????????????????????????????????????????????????????ICAS?????????????????????????????????????????FeliCa?????????????????????? FeliCa?????????????????????????????????????????????????????????????/???????????????????????????????????????????ICAS??????????? DXC Japan??ICAS?????????????2005??ICAS??????????????FeliCa????????????????????????.

Security Affairs
JANUARY 25, 2023
According to the notice, threat actors had access to an older database of customers who had signed up for the Zacks Elite product between November 1999 through February 2005. Zacks Investment Research (Zacks) disclosed a data breach, the security may have exposed the data of 820K customers. ” reads the notice of data breach.
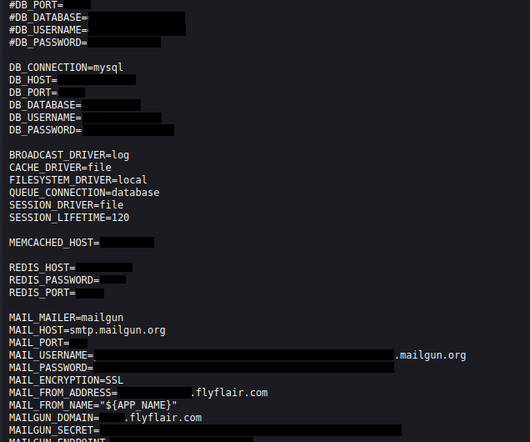
Security Affairs
SEPTEMBER 26, 2023
Flyflair.com belongs to the Canadian ultra-low-cost carrier Flair Airlines, founded in 2005. The leak consisted of publicly accessible environment files hosted on the flyflair.com website. According to SimilarWeb, the website attracts 3.2 million monthly visitors. The Cybernews research team discovered the leak on February 27th, 2023.

Security Affairs
JUNE 13, 2023
According to the notice, threat actors had access to an older database of customers who had signed up for the Zacks Elite product between November 1999 through February 2005. The company discovered the intrusion at the end of 2022, it believes the unauthorized access took place sometime between November 2021 and August 2022.
Hunton Privacy
JUNE 30, 2023
APEC CBPR and PRP operationalize the nine Privacy Principles set forth in the 2005 APEC Privacy Framework. On June 26, 2023, the Centre for Information Policy Leadership (CIPL) published the third edition of its Frequently Asked Questions on Cross-Border Privacy Rules, Privacy Recognition for Processors, and Global CBPR and PRP (FAQs).

Hunton Privacy
JUNE 13, 2019
The adaption of French law to the new EU data protection framework was conducted in various stages: The French Data Protection Act of January 6, 1978, was first amended by a law dated June 20, 2018, while its implementing Decree of October 20, 2005, was amended by a Decree of August 1, 2018.

Security Affairs
MARCH 27, 2022
The oldest flaws in the set of 66 recently added issues are dated back to 2005. The US Cybersecurity and Infrastructure Security Agency (CISA) added 66 new flaws to its Known Exploited Vulnerabilities Catalog. The new vulnerabilities added to the catalog have to be addressed by federal agencies by April 15, 2022.
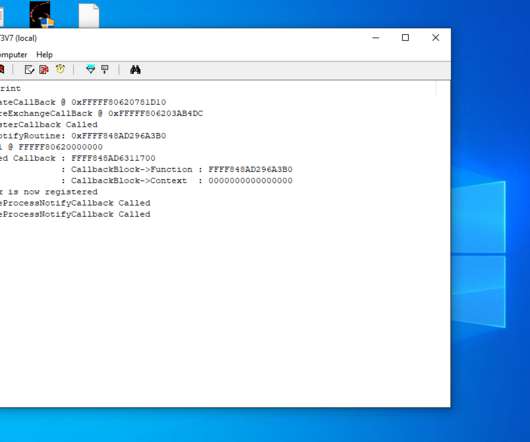
Security Affairs
MAY 31, 2021
The feature was first introduced in 2005 with the x64 editions of Windows XP and Windows Server 2003 Service Pack 1. Kento published technical details of its attack in a blog post and also released proof-of-concept (PoC) code for his attack. ” reported The Record. . ” reported The Record.

Adapture
SEPTEMBER 19, 2023
About Smartsheet Since its founding in 2005, Smartsheet enables individuals and teams to become high achievers by creating innovative work management solutions, mobilizing a passionate and diverse global team, and redefining the possibilities of work management, empowering people to do amazing things.
Krebs on Security
JUNE 1, 2023
ru , which DomainTools.com says was registered in 2005 to a Konstantin E. Megatraffer has continued to offer their code-signing services across more than a half-dozen other Russian-language cybercrime forums, mostly in the form of sporadically available EV and non-EV code-signing certificates from major vendors like Thawte and Comodo.

Security Affairs
MAY 3, 2023
The platform has been active since 2005, according to the DoJ, it generated tens of millions of dollars in revenue. Authorities dismantled the Try2Check platform, a Card-Checking platform that generated tens of millions of dollars in revenue. DoJ charged the Russian citizen Denis Gennadievich Kulkov with running the Card-Checking services.
Security Affairs
MARCH 28, 2023
million records dating back to at least 2005 were also compromised in the data breach. million records dating back to at least 2005 were also compromised in the data breach. Australian loan giant Latitude Financial Services (Latitude) revealed that a data breach its has suffered impacted 14 million customers. 94% of these records (5.7
John Battelle's Searchblog
JANUARY 5, 2023
I’m likely guilty of turning Kevin into a Yoda-like figure – he was a mentor to me in the early years of the digital revolution. But the idea rings true – and it lies at the heart of the debate around artificial intelligence and its purported impact on our commonly held beliefs around literacy. ” Indeed.

Adam Levin
MAY 24, 2019
Google announced a glitch that stored unencrypted passwords belonging to several business customers, a situation that had been exploitable since 2005. This issue has been fixed and, again, we have seen no evidence of improper access to or misuse of the affected passwords.
Security Affairs
JULY 24, 2020
It was formed in 2005 in response to European Union requirements to separate the natural monopoly of infrastructure management from the competitive operations of running train services. The company has over 13,000 employees for a revenue of around $8 Billion. “We We will continue to download your data until you contact us.”.
Security Affairs
APRIL 3, 2021
The security breach data breach took place on March 22nd and 23rd, the hacker accessed information of customers who had applied for a credit card between 2005 and 2019. District Court in Seattle. Based on our analysis to date, this event affected approximately 100 million individuals in the United States and approximately 6 million in Canada.

Hunton Privacy
APRIL 2, 2015
The new website fulfills the agreement made between Commissioners “to create a permanent website in particular as a common base for information and resources management” in the Montreux Declaration adopted in 2005.

Information Management Resources
JANUARY 12, 2018
Researchers began writing about the potential for security weaknesses at the heart of central processing units, or CPUs, at least as early as 2005.

AIIM
NOVEMBER 30, 2017
But after 2005, these effects vanish from the measured statistics. Total productivity growth has fallen by two-thirds since 2005, while real GDP growth has averaged about 2 percent per year—all during a period in which the digital economy has continued to grow.”. I came across a chart recently that left me scratching my head.

The Last Watchdog
MARCH 28, 2023
Over my career, I have created three non-profits and two SaaS for profits, one of which I sold in 2005. Even if you managed to get a range of certifications which show that you have some skills, finding a job in your field is extremely unlikely because the market is so small and undeveloped. It is not enough to just educate the students.
Security Affairs
APRIL 19, 2020
” Webkinz were originally released by the Canadian toy company Ganz on April 29, 2005. Webkinz are stuffed animals that have a playable online counterpart, www.webkinz.com, in “Webkinz World.” On Webkinz World, the Secret Code allows the user to own a virtual version of the pet for online play. .

Imperial Violet
AUGUST 25, 2021
The 2005 edition changed that to be ISO/IEC 8859-1 (i.e. Segments are bitstrings, concatenated without any byte-alignment, and terminated with an empty segment of type zero. If you want to squeeze the maximum amount of data into a QR code without it turning into a gray square, understanding segmentation helps.

John Battelle's Searchblog
FEBRUARY 17, 2013
The company I started in 2005 has been executing native programs since 2005. The post Reporters Need to Understand Advertising. But Should They Be Making It? appeared first on John Battelle's Search Blog. image ) I know that when I do write here, I tend to go on, and on – and those of you who read me seem to be OK with that.

The Security Ledger
NOVEMBER 3, 2021
Programs like iDefense Labs Vulnerability Contributor Program (VCP) (launched in 2002) and TippingPoint’s Zero Day Initiative (2005) were accused -at the time- of incentivizing the work of criminals and bad actors. . When the first bugs for cash programs emerged almost two decades ago, they were controversial.

The Schedule
DECEMBER 10, 2019
In 2005, two people working in Records and Archives at the World Health Organisation — Ineke Deserno and Donna Kynaston — had this to say about the intersection of records management and archival work: “A records management program is indispensable for an archives program. It ensures.
Krebs on Security
JULY 25, 2023
And a great many of these “proxy” networks are marketed primarily to cybercriminals seeking to anonymize their traffic by routing it through an infected PC, router or mobile device. “We created a fingerprint to identify the call-back infrastructure for SocksEscort proxies,” Spur co-founder Riley Kilmer said.
Expert insights. Personalized for you.
We have resent the email to
Are you sure you want to cancel your subscriptions?



Let's personalize your content