Experts warn of threat actors abusing Google Alerts to deliver unwanted programs
Security Affairs
FEBRUARY 21, 2021
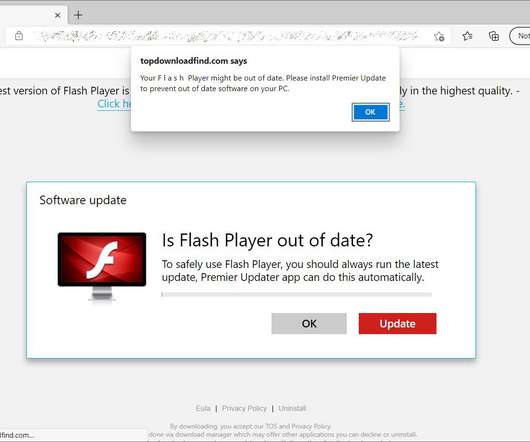
Experts warn of threat actors using Google Alerts to promote a fake Adobe Flash Player updater that delivers unwanted programs. Experts from BleepingComputer are warning of threat actors that are using Google Alerts to promote a fake Adobe Flash Player updater that delivers unwanted programs. Bad actors publish posts with titles containing popular keywords to allow Google Search to index the content.












Let's personalize your content