US CISA Aims to Expand Automated Malware Analysis Support
Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.
 Analysis Related Topics
Analysis Related Topics 
Data Breach Today
APRIL 10, 2024
US Cyber Defense Agency Scales Next-Generation Malware Analysis Platform The U.S.

Data Breach Today
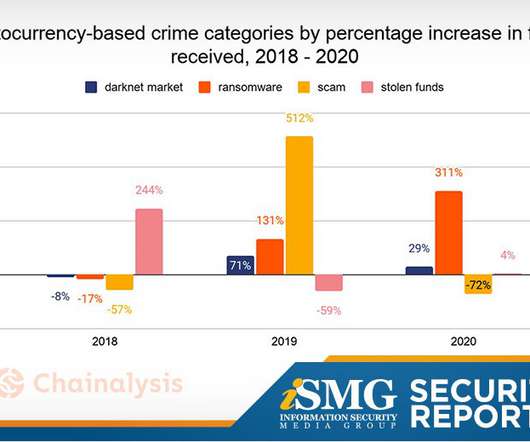
JANUARY 29, 2021
The latest edition of the ISMG Security Report features an analysis of this week’s police takedowns of Emotet and Netwalker cybercrime operations. Also featured: Updates on passwordless authentication and the use of deception technology.
This site is protected by reCAPTCHA and the Google Privacy Policy and Terms of Service apply.
Data Breach Today
FEBRUARY 5, 2021
The latest edition of the ISMG Security Report features an analysis of the persistent threat of ransomware. Also featured: Sorting out breaches tied to Accellion’s File Transfer Appliance; an update on fraud trends in 2021.

Data Breach Today
SEPTEMBER 3, 2021
The latest edition of the ISMG Security Report features an analysis of data breach trends. Also featured: yet another Microsoft Exchange vulnerability and misconceptions about cybercrime groups.
Advertiser: ZoomInfo
Download this ebook to learn how to maintain a strategy that includes refreshed information, database cleanses, and an accurate analysis at the same time. Forward-thinking marketing organizations have continuously invested in a database strategy for enabling marketing processes.

Data Breach Today
DECEMBER 18, 2020
The latest edition of the ISMG Security Report features an analysis of what we know so far about the impact of the SolarWinds supply chain hack and how to respond.

Schneier on Security
JANUARY 2, 2024
This is a serious analysis, and the methodology looks sound.) Future research should aim towards a more comprehensive analysis to determine the potential influence of TikTok on popular public narratives. TikTok seems to be skewing things in the interests of the Chinese Communist Party.

Advertisement
A good data story is formed by three components: Data analysis - This is the basis of a strong story and mastering the data is an essential part of the process. Data-driven storytelling could be used to influence user actions, and ensure they understand what data matters the most.

Advertisement
Data aware: Users can combine past experiences, intuition, judgment, and qualitative inputs and data analysis to make decisions. Data literate: Users have a comfort level of working with, manipulating, analyzing, and visualizing data. Download the eBook to learn about How to Build Data Experiences for End Users.

Advertisement
Just by embedding analytics, application owners can charge 24% more for their product. How much value could you add? This framework explains how application enhancements can extend your product offerings. Brought to you by Logi Analytics.

Advertisement
Why do some embedded analytics projects succeed while others fail? We surveyed 500+ application teams embedding analytics to find out which analytics features actually move the needle. Read the 6th annual State of Embedded Analytics Report to discover new best practices. Brought to you by Logi Analytics.

Advertisement
Many application teams leave embedded analytics to languish until something—an unhappy customer, plummeting revenue, a spike in customer churn—demands change. But by then, it may be too late. In this White Paper, Logi Analytics has identified 5 tell-tale signs your project is moving from “nice to have” to “needed yesterday.".

Advertisement
Think your customers will pay more for data visualizations in your application? Five years ago they may have. But today, dashboards and visualizations have become table stakes. Discover which features will differentiate your application and maximize the ROI of your embedded analytics. Brought to you by Logi Analytics.

Speaker: Blackberry, OSS Consultants, & Revenera
Without establishing Software Composition Analysis best practices and the ability to produce a Software Bill of Materials, companies are most likely leaving a gaping hole in their software supply chain for bad actors to slip in and take advantage of vulnerabilities.
Advertisement
For 12 years Dresner Advisory Services has run analysis on the importance of business intelligence, and the different providers of embedded BI solutions. You’ll learn: Analysis and Trends on Business Intelligence Users. You’ll learn: Analysis and Trends on Business Intelligence Users. Industry and Vendor Analysis.
Let's personalize your content